Kali Linux Tools ListThe Kali Linux tools list is a collection of tools included in the Kali Linux distribution that help users execute penetration testing and explain why Kali Linux is the most widely used ethical hacking distribution worldwide. However, the tool's utilization is not limited to ethical hacking: many of these tools are effective and worthwhile for a webmaster. These tools assist users in penetration testing by allowing them to perform tasks such as testing, hacking, and other aspects of digital forensics. The list we will discuss here caters to the top tools in Kali Linux, regardless of who uses them or the specifics of their utility space. List of Kali Linux Tools and Description of EachIn Kali Linux, there are various tools that come pre-installed with Kali Linux, which we will discuss. If we are unable to find any pre-installed tool in distribution, we can easily download and install them to utilize them for the utility! We will ensure that the list we've provided covers all aspects of the penetration testing cycle, including reconnaissance, scanning, Exploitation, post-exploitation. We'll try to concentrate on a few key tools, as discussing them all would be an unending conversation due to the limitlessness of tools present. Without further ado, let's get started on the list, which has been divided into sub-groups based on its utility: 1. Gathering Information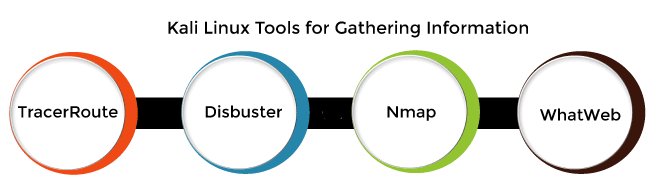
The following are the Kali Linux tools that we used for gathering information: TracerRoute This is a utility in Kali Linux that allows users to do network diagnostics. It displays the connection route and measures the time it takes for packets to travel across an IP network. Dirbuster As the name suggests, this tool is used to find hidden objects, files, and even directories on a website. A dictionary-based attack is launched with a set of preconfigured lists of words, and the response is analyzed to find the hidden gem! Nmap Nmap, a network discovery and security auditing tool, is another frequently used tool. There are options that notify every open port on the target. The Nmap ("Network Mapper") tool is used in active reconnaissance to discover not only the live systems but also gaps in the system. This versatile tool is well supported and one of the best in the hacking community. Nmap is available for all operating systems and includes a graphical user interface. It is used to identify network flaws. WhatWeb This tool facilitates information gathering and functions similarly to a website fingerprint. It's like an interrogator agent attempting to extract information from a website to determine what that website is made of. There are 1800 plugins available to help WhatWeb, each with its own set of features. 2. Password Attacks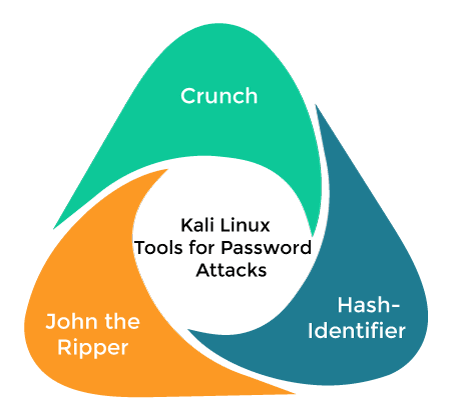
The following are the Kali Linux tools that we used for password attacks: Crunch This tool functions similarly to a utility, allowing users to generate personalized wordlists. For the purpose of password attacks, various sorts of permutations and combinations are generated using a standard character set or a predefined one. John the Ripper John the Ripper is another popular offline password cracking service that bundles several password crackers into one package. It handles customization cracker, hash type, and many other tasks, all while operating in offline mode! Hash-identifier With the help of this tool, users can identify different hashes used to encrypt data and passwords. Another tool, Findmyhash, is used in conjunction with this tool to crack data utilizing web service. Suppose we get an encrypted text; it is put through a hash-identifier to find the hash type associated with it. Then Findmyhash later cracks the data into its original string. 3. Spoofing and Sniffing
The following are the Kali Linux tools that we used for spoofing and sniffing: BetterCAP Another excellent tool for launching man-in-the-middle attacks on a network. This is accomplished by manipulating HTTP, HTTPS, TCP traffic in real-time, credential sniffing, and others to carry out such attacks! Wireshark This is yet another excellent and commonly used network analyzer for security auditing. Wireshark uses display filters to conduct general packet filtering, which includes grabbing a captured password. 4. Wireless Attack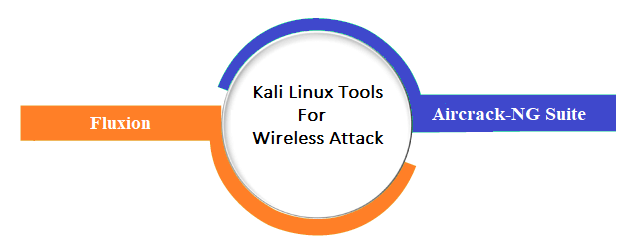
The following are the Kali Linux tools that we used for a wireless attack: Fluxion It's the same as making a clone of the target Wi-Fi network. When a user connects to the wireless network, an authentication window pops up, and the user enters the password, which is then captured! Aircrack-NG Suite: As the name implies, this is a suite that includes a scanner, WEP and WPA/WPA2-PSK cracker, packet sniffer, and analysis tool that work together to crack or find vulnerabilities in any wireless medium! 4. Analysis of Vulnerability Nikto One of the most common tools for assessing security threats and vulnerabilities. This utility has the capacity to scan over 6500 files or programs that could be harmful. 5. Keeping AnonymityThe tool which we used for keeping anonymity is: 
MacChanger When someone is doing the various actions described above, we must ensure that our identity is not disclosed, and it would be unwise if any prevention is overlooked. This tool allows us to change the user's MAC address in order to keep our identity hidden! 6. Assessing Database
The Kali Linux tool which we used for accessing database is: SQLMap This is one of the most extensively used tools for database evaluation as the process of detecting and exploiting SQL injection vulnerabilities that can lead to database takeover. We may need to identify a website that is SQL injection vulnerable to continue with this, for which another tool discussed above, SQLiv, will come in handy! 7. Analysis of Web Application
The following are the Kali Linux tools that we used for a web application: BurpSuite BurpSuite is another addition to web application analysis that consists of a group of tools that are bundled to form a unified suite of web application security testing starting from scratch, i.e. the analysis of the attack surface. Web apps can use this tool to test the security of their infrastructure. Through the discovery of potential security flaws and exploits, it will map and evaluate the attack surface of the targeted web app. Its main feature is that it can act as a proxy interceptor, allowing it to hijack the traffic that exists between a web server and a web browser. OWASP-ZAP OSASP-ZAP is a Java-based tool for testing the web application's security, featuring an intuitive GUI for operations such as fuzzing, spidering, scripting and so on, as well as a number of plugins to make the process easier. SQLiv This is one of the most widely used tools for easy and large-scale vulnerability scanner of SQL injection. This is one of the few on the list that isn't pre-installed in the Kali Linux distribution, but it is still the most popular!
Next TopicHow to install AnyDesk on Kali Linux
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










