Linux hosts (file)The host (computer file) is an OS file that can map the hostnames to the IP addresses. This file is a plain file of the text. A file originally named HOSTS.TXT and was maintained manually and made present by file sharing for the ARPANET membership via Stanford Research Institute. It is including the addresses and hostnames of hosts as shared for ad-dition via member organizations. In 1983, the Domain Name System was first described and implemented 1984. It auto-mated the process of publication and facilitated dynamic and instantaneous hostname resolution within a highly growing network. The hosts file is an alternative mechanism of name resolution and it is configurable of-ten as the facilities part like the Name Service Switch as the fallback method or the pri-mary method in the current operating system. Purpose of the hosts fileThe hosts file is a system facility that assists to address network nodes within the com-puter network. It is a basic part of an Internet Protocol implementation of an operating system. It serves the function of converting hostnames (human-friendly) into various numerical protocol addresses which are known as IP addresses that recognize and find a host within an IP network. Preferentially, the hosts file content is used to other methods of the name resolution in a few operating systems like Domain Name System. However, several systems operate name service switches (nsswitch.conf for Unix and Linux) for providing customization. The hosts file is upon the direct control of the local administrator of the computer, un-like remote Domain Name System resolvers. File Content of hosts fileThe hosts file includes a text line consisting of the IP address within the initial files of text followed by multiple host names. All fields are isolated by white space and tabs are preferred for various historical reasons. However, the spaces are used as well. Comment lines might be included. These lines are represented by the # (octothorpe) symbol in the initial position of the lines. Besides, the black lines are entirely ignored in the file. For example, a hosts file typically include the below: The above example only includes entries for the system's loopback addresses and the host names and the hosts file's typical default content. The example represents that the IP address might have more than one host name (loopback and localhost) and a host name might be mapped to both IPv6 and IPv4 IP addresses as displayed respectively in the second and first lines. Location within the File SystemIn the file system hierarchy, the hosts file's location varies by OS. Usually, it is named as hosts without any extension.
History of the Hosts FileThe Internet predecessor, i.e., ARPANET had no shared database of the host name. All network nodes managed their map of many network nodes as required and assigned the names that were memorable to the system users. There was no mechanism to ensure that each reference to a provided node within the network was applying a similar name. Also, there is no mechanism for reading the hosts files of other computers for automatically obtaining a copy.
Extended Applications of the Hosts FileThe hosts file might be used for defining any domain name or hostname for applying in-side the local system in its resolving host names function.
A few intranet and web service administrators and developers describe locally specified domains within a LAN for several objectives like accessing the internal resources of the company and for testing local websites in advancement.
In the hosts file, the entries might be the domains of familiar malicious servers and re-sources that include adware, spyware, and other malware or used for blocking online advertising. It might be archived via including entries for many sites for redirecting the requests to other addresses that don't available or to any harmless target like the local machine. Various trading software applications may be used for populating the hosts file along with entries of automatically familiar undesirable Internet resources. Various user-made hosts files which disable or block the nuisance servers are available publicly in addition. Fravia specified these types of files as "powerful", "precious", and "scrolls" in his anti-advertisement pages in which this hosts usage was published first.
A few pirated versions of software depend on a changed hosts file for preventing the software from contacting the publisher activation servers. Sometimes, activation serv-ers however occur in normal objective hosts files. Security issues of the Hosts FileThe hosts file might prevent a thrash vector for mischievous software. This file might be changed, for example, by trojan horse, computer viruses, or adware software for redi-recting the traffic through the desired target to sties hosting unwanted or malicious con-tent. The general computer worm Mydoom.B disabled or blocked the users from accessing sites about antivirus software and computer security. Also, it affects the access through the computer (compromised) to the Microsoft Windows Update website. Malware has changed the library, liable to load the hosts file for redirecting it to any file, it can freely control in a few cases. Format of the Hosts FileIn the hosts file, the entries have the below format: The domain names and IP addresses must be isolated by one tab or space at least. The lines beginning with the # symbol are comments and avoided. We can simply open a file in our text editor for adding an entry to a hosts file. The hosts file modifications quickly take effect in situations where the entries of Domain Name System are cached via applications. We can simply open a file and delete the lines we added to undo the modifications. Change the Hosts FileIn Linux, /etc/hosts is the complete path to a file. The following instructions are valid for every distribution of Linux including Linux Mint, Debian, RHEL, CentOS, and Ubuntu: 1. Open a hosts file with our favorite text editor in our terminal window: Enter the password for sudo when asked. 2. Scroll down the file's end and add our newer entries: 3. Save the modifications. 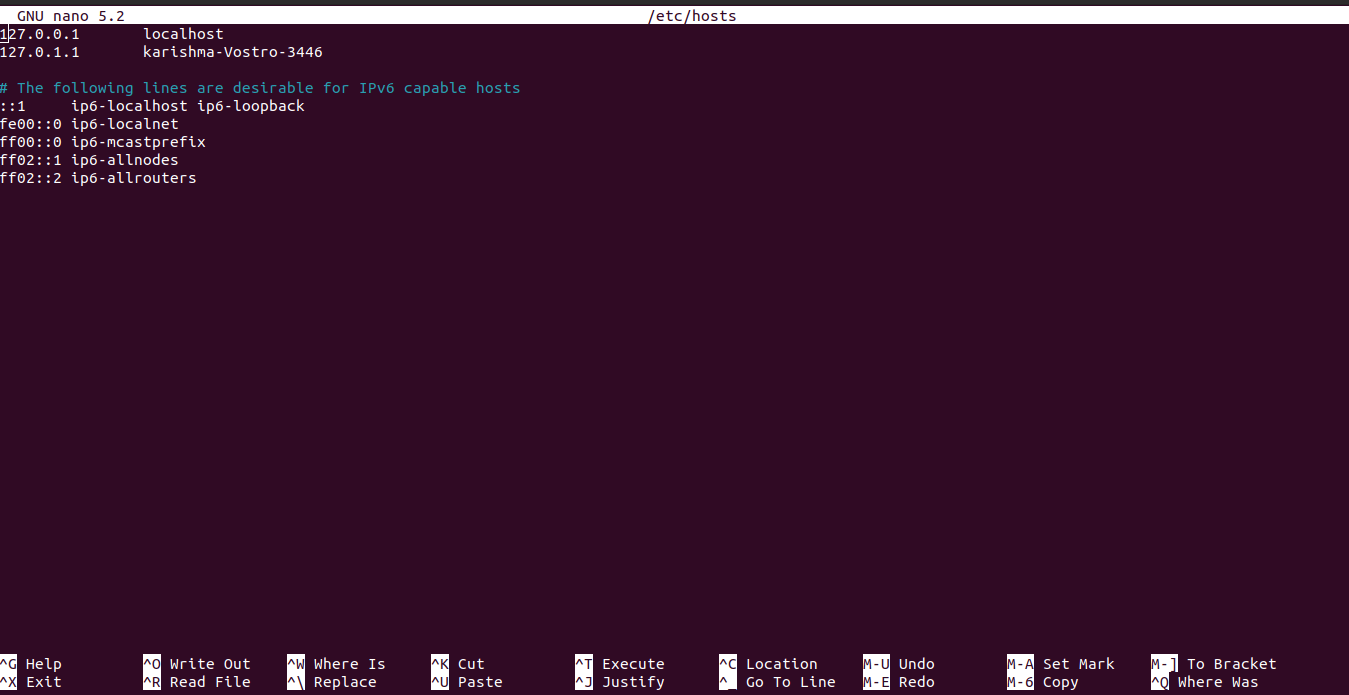
Next TopicUNIX operating system
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










