Metasploit InterfaceTo perform Metasploit's underlying functionality like the command line, graphical interface, and console, it provides more than one interface. The internal functions of the Metasploit framework have direct access provided by utilities. If we want to exploit development, these utilities are invaluable. These utilities will also be invaluable when we don't want the flexibility of the entire framework. We can access the Metasploit framework in different ways like MsfGUI, Armitage, Msfconsole, Metasploit Pro, Msfweb, and Msfcli. MSFconsoleThe Metasploit framework has the most popular part, named Msfconsole. Within the framework, this type of tool is well-supported, feature-rich, and most flexible. In a framework, a handy all-in-one interface exists, which is provided by Msfconsole to almost every setting and option. It is just like that our exploitation dreams have a one-stop-shop. Using the Msfconsole, we can do anything against the entire network like performing enumeration, launching an exploit, creating listeners, loading auxiliary modules, or running mass exploitation. If there is constantly changing in the Metasploit framework, the command's subnet remains relatively constant. We can keep up with any changes if we have done mastering in basics of msfconsole. The msfconsole is important in almost every part of this tutorial. 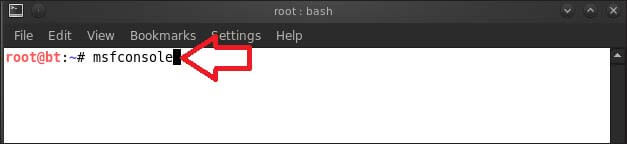
Now we can enter any command in which we are interested with the help command to access the help files of msfconsole. Suppose we want to communicate with the host, we can use help for the connect command, which is shown in the following screenshot. The lists of resulting documentation contain the tools description, usage, and various option flags. We can put msfconsole followed by -h to access all the help files of msfconsole. After executing this command, the resulted list of documentation will look like this: MSFcliIn order to provide access to the framework, the different approaches are used by Msfconsole and Msfcli. The msfconsole provides a very interactive, user-friendly way to access all features. While scripting is put as a priority by msfcli and it also puts interpretability with other tools which are based on the console. It uses a command line to run directly instead of using a unique interpreter for framework. Using the command line, we can redirect into msfcli from other tools, and it directs the output of msfcli to other command-line tools. The launch of auxiliary modules and exploits are also supported by Msfcli. For the framework, if the new exploits are developed and modules are tested, it will be convenient. If we know about the options and exploits which we need for unique exploitation, it will become a fantastic tool. The msfconsole is more forgiving as compared to the msfcli. Msfcli offers a command msfcli -h to provide some basic help, as shown here: If we are learning about the Metasploit and get stuck somewhere, we can add the letter O to the string's end at whichever point we found any problem. Using this letter, we are able to see all the available options in a module. For example, assume that we are stuck in module ms08_067_netapi. Now we will add the letter O after the module to see the available options as follows: The above execution specifies that three options are required by the module, i.e., RHOST, RPORT, and SMBPIPE. Now we will see the available payloads by adding a P as follows: For our exploit, all the required options are set. Now at the end of msfcli argument string, we will add the letter E and run our exploit as follows: In the above execution, from the remote system, we have successfully received a Window command prompt. ArmitageMetasploit has a component named Armitage. It is created by Raphael Mudge, and it contains a graphical user interface, which is very interactive. This user interface is freely available, feature-rich, and highly impressive. In this tutorial, we will not talk about armitage in-depth, but it has many things that are worth mentioning to explore. In this section, we will learn about the ins and outs of Metasploit. If we are able to understand the working of framework, GUI will become awesome for us. We will run the armitage command to launch the armitage. At the time of startup, we have to select Start MSF. Using this, Metasploit instance and armitage can be connected. When the armitage is starting running, we can click on the menu to access other Metasploit functionality and perform a particular attack. For example, the browser (client-side) exploits are shown in the following screenshot: 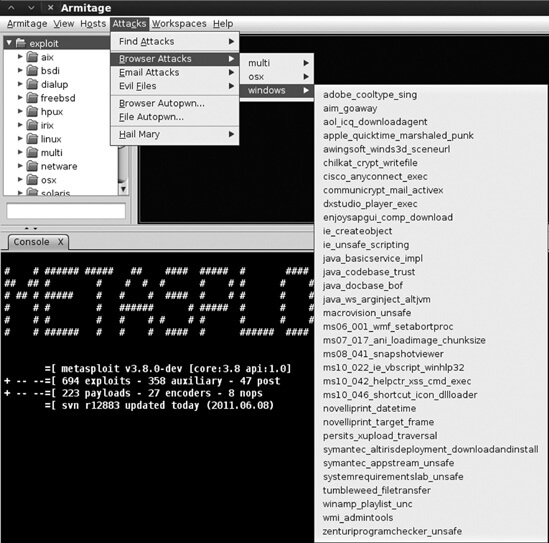
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










