Reflexive Access ListAn access-list by default doesn't record the sessions. The many permit and deny rules that make up an access list are read from top to bottom. No additional condition is met if any of the criteria are met, hence it is executed. A reflexive Access-list serves as a stateful firewall for a very small workplace by only allowing traffic that is initiated within the network while blocking other packets coming from the outside. 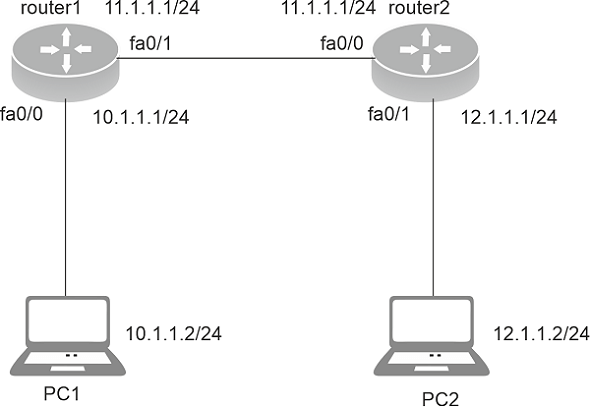
Reflexive Access List -Reflexive Access-list is an access-list that only accepts answers to packets from network sessions that have already been started (from the outside network). Working of Reflexive Access List -Reflexive Access-list are activated when a session begins inside the network and leaves the network through the router (operating reflexive Access-list). As a result, it makes a temporary entry for traffic that originates inside the network and only permits outside traffic that is necessary for the session (traffic generated within the network). When the session is over, this transient entry is deleted. Characteristics Of Temporary Entry -
Characteristics of Reflexive access-list -
Configuration -There are two routers: router1 (IP address: 10.1.1.1/24 on fa0/0 and 11.1.1.1/24 on fa0/1), router2 (IP address: 11.1.1.2/24 on fa0/0 and 12.1.1.1/24 on fa0/1) and two PCs (IP addresses: 10.1.1.2/24" and 12.1.1.2/24," respectively). To enable pinging between PCs, we will first provide routes using EIGRP to all of the routers. Configuring Eigrp on router1: Configuring Eigrp on router2: At this point, we'll permit IP, TCP, and UDP traffic from within the network (10.1.1.0 network) and assess traffic arriving from outside the network (12.1.1.0 and 11.1.1.0 network). Making an access list with the name "reflexive" for inside traffic leaving. Here, IP, TCP, and UDP communication is permitted, and they are designated as the ip database, tcp database, and udp database, respectively. Reflexive is not a keyword in this context; it is the name of the Access-list. Apply this Access-list now to router1's int fa0/1's outbound so that traffic leaving the router will be permitted. Apply an access list now for internal network traffic, also known as inbound traffic. Only that communication, which is started by the internal (10.1.1.0) network, should be allowed to enter. Since we have enabled Eigrp traffic here, the routers should be able to communicate with one another; otherwise, no traffic will be able to return to the ether network. In order to allow traffic that has been started inside the network using TCP, UDP, or IP, we have evaluated the udp databse, ip database, and tcp database. Apply this now in the inside direction of interface fa0/1 so that the traffic coming in can be assessed. The Access-list in this case is called reflexive in. Benefits -The reflexive Access-list has the following benefits:
The disadvantage
Next TopicSynchronous Optical Network (SONET)
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










