Spanning Tree ProtocolThe spanning tree protocol is also known as STP. It is a protocol that monitors the overall performance of the network. The main task of the spanning tree protocol is to remove the redundant link. This protocol uses the Spanning tree algorithm (STA), which is used to detect the redundant link. The STA maintains the topology database that is used to find the redundant links. If the redundant link is found, then the link gets disabled. Once the redundant links are removed, then only those links will remain active which are chosen by the STA. If a new link is added or some existing link is removed, then the STA will be re-executed to adjust the changes. Before understanding the spanning tree protocol, we first looked at the complete graph and spanning tree. A complete graph is a graph in which a line connects each pair of vertices. In other words, we can say that all the points are connected by a maximum number of lines. In computer networking, the complete graph can also be said as a fully meshed network. Let's understand the complete graph through an example. Suppose there are three points, i.e., A, B, and C. Three lines connect these three points. A line connects every two-point, and we get a complete graph. 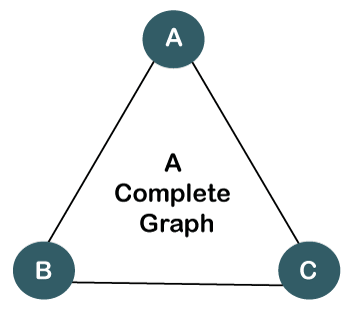
The complete graph is formed when a maximum number of lines connects all the points, whereas the spanning tree is formed when a minimum number of lines connects all the points. From the above complete graph, we can get three spanning trees. 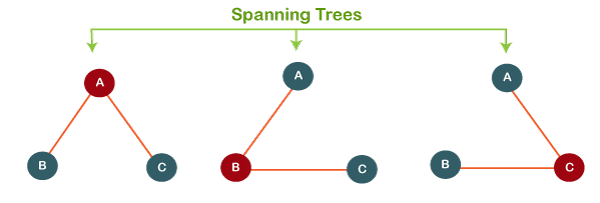
Till now, we have observed two basic features of spanning-tree:
What is a spanning tree protocol?The spanning tree protocol is a layer 2 protocol that tends to solve the problems when the computers use the shared telecommunications paths on a local area network. When they share the common path, if all the computers send the data simultaneously, it affects the overall network performance and brings all the network traffic near a halt. The spanning tree protocol (STP) overcomes this situation by using the concept of bridge looping. Bridge looping is used when there are multiple connections between the two endpoints, and messages are sent continuously, which leads to the flooding of the network. To remove the looping, STP divides the LAN network into two or more segments with the help of a device known as bridges. The bridge is used to connect the two segments so when the message is sent, the message is passed through the bridge to reach the intended destination. The bridge determines whether the message is for the same segment or a different segment, and it works accordingly. This network segmentation greatly reduces the chances of a network coming to a halt. How spanning tree protocol works?The following are the steps that spanning tree protocol uses:
Ports in STPThere are five ports used in STP:
Let's understand through an example. 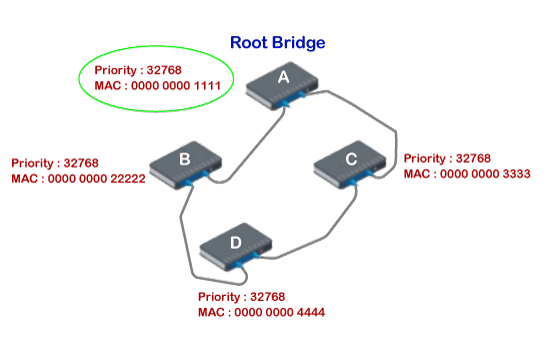
Suppose there are four switches A, B, C, and D on a local area network. There are redundant links that exist among these interconnected devices. In the above figure, there are two paths that exist, i.e., DBA and DCA. Link redundancy is good for network availability, but it creates layer 2 loops. The question arises "how network blocks the unwanted links to avoid the loops without destroying the link redundancy?". The answer to this question is STP. First, STP chooses one switch as a root bridge. In the above case, A switch is chosen as a root bridge. Next, other switches select the path to the root bridge, having the least path cost. Now we look at the switch B. For switch B, there are two paths that exist to reach switch A (root bridge), i.e., BDCA and BA. The path BDCA costs 7 while the path BA costs 2. Therefore, path BA is chosen to reach the root bridge. The port at switch B is selected as a root port, and the other end is a designated port. Now we look at the switch C. From switch C, there are two paths that exist, i.e., CDBA and CA. The least-cost path is CA, as it costs 1. Thus, it is selected as a root port, and the other end is selected as a designated port. Now we look at the switch D. For switch D, there are two paths that exist to reach switch A, i.e., DBA and DCA. The path DBA costs 4 while the DCA costs 5. Therefore, path DBA is chosen as it has the least cost path. The port on D is selected as a root port, and on the other end, switch B is selected as a designated port. In this example, we have observed that the root bridge can contain many designated ports, but it does not contain a root port.
Next TopicOSPF Protocol
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










