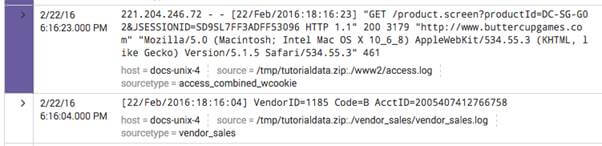
Splunk Event TypesIn this section, we are going to learn about the Event types in the Splunk. We will also learn about the Event types and the search time sequences, search time operation order, how event type works, event type tags and saving a event type. Event TypesEvent forms are a framework for categorizing the data to help us make sense of it. Event types allow us to sift through enormous amounts of data, find similar patterns, and create alerts and reports. Note: It is not recommended to use the event forms as a short cut for the quest. If we want a portion of a search shortened, using a search macro is much better. Search macros are more versatile in what they can express, they can include other search commands and not just base query words, they can be parameterized, and when events are retrieved do not incur costs. This can also be easier to handle since a single search macro can take various types of events.Event types and the search-time sequenceWhen we run a search, Splunk software runs multiple operations to derive objects of knowledge and apply them to events returned by the search. Splunk program performs these operations in a fixed sequence. Search-time operations orderTypes of events come seventh in the order of search-time activities, before tags but after lookups. RestrictionsSplunk software processes the types of events first through priority score and then through ASCII sort order. Search strings defining event types cannot reference tags, because event types are always processed before tags and added to events. How event types workAny event that may be returned by that search becomes associated with that type of event. Say we have that search, for example: sourcetype=access_combined status=200 action=purchase If we save that search as an event type named successful purchase, eventtype = successful_purchase will be added at search time to any event that can be returned by that search. This happens even though we're looking for something entirely different. Note: Using event types will consume a lot of data, as every search attempt to associate events with some known form of event. As more types of events are defined, the cost of performing searches increases. Using the command.search.typer parameter, we can examine the execution costs of search commands. See inspector for search job.Use eventtype = successful_purchase as a search term to create a search that works for events that match that type of event. A single event can match different types of events. Eventtype acts as a multi-value field when an event matches two or more types of events. Significant event type definition restrictionsWe cannot base the form of an occurrence on a quest to:
The last point is not a rigid restriction but a best practice. We want to avoid situations where another user modifies the search string underneath failed_login_search at a future date, possibly in a way that breaks the type of event. If we use actual search strings in its definition, we have more control over the ongoing validity of the event type. Note: Use a search macro if we want to use the event forms as a way to cut our quest short.Creating event typesThe easiest way of generating a new form of event is through Splunk Internet. Click Save As and select Type of Event after we run a search that would make a good type of event. This opens the Save as Type Event window, where we can include the name of the event form and optionally add tags to it. See Identifying and keeping event types in Splunk Web for more detail on saving searches as event types. Event type tagsEvent types can associate them with one or more tags. These tags can be applied when saving a search as an event form and from the event type manager, located in Settings > Event types. From this window's list of event types, choose the one we wish to edit. Label types of events to group the data into categories. Multiple tags can be given per case. In Splunk Web, we can tag an event type, or configure it in tags.conf. For more information regarding the tagging of the event type. Event type tags example 1By giving them more descriptive names, use event type tags to track abstract field values such as HTTP access logs, IP addresses, or ID numbers. Add tags to type of event by going to Settings > Types of events. In this menu, pick the type of event from the list of event types. After adding tags to our types of events, search for them in the same way we search for any tag. Let's say we saved a search for page not found as the status=404 event type and then saved a search for failed authentication as the status=403 event type of event. If we tagged any of these event types with an HTTP client error, we can recover all events of any of those event types by using the search: tag::eventtype=HTTP client error Event type tags example 2The common information model (CIM) add-on for the Splunk platform usually uses event type tags to normalize newly indexed data from an unfamiliar source type. We may use tags to identify various types of events within a single source of data. We can apply CIM-compliant tags to our data.
Defines types of events on Splunk WebA type of event describes a search returning a specific type of event or a valuable set of events. Any event that may be returned by that search becomes associated with that type of event. Say we have that search, for example: sourcetype=access_combined status=200 action=purchase If we save the search as an event type called successful_purchase, event type = successful_purchase will be applied at search time to any event that may be returned by that search. This happens even though we're looking for something entirely different. And later, if we want to create a search that works for events that suit the type of event, include in the search string eventtype = successful_purchase. A single event can match different types of events. Eventtype functions as a multivalue field when an event matches two or more forms of event. Save a search that we ran as a form of event.We can save that search as an event type when we execute a search. Types of events typically reflect searches that return a specific event or return a useful variety of events. Once we build an event type, in $SPLUNK_HOME / etc / users/<your-username>/<app>/local/, the event type description is applied to eventtypes.conf, where < app > is the current device context. The Splunk framework will shift the event type to $SPLUNK_HOME / etc / apps/<App>/local/ if we change the permissions on the event type to make it accessible to all users (either in the app, or globally for all apps). Save search as a type of event.
Any type of event we generate with this method will also appear in Settings on the Event Types listing tab. The event form can be changed on the Event Types listing tab.
Next TopicSplunk Create a basic chart in Splunk
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share