Ubuntu AntivirusWhat is Antivirus?Anti-virus software is also called anti-malware. It is a computer program used for preventing, detecting, and removing malware. Originally, anti-virus software was developed for detecting and removing computer viruses so the name. Although, antivirus software began for protecting from many threats of computer with the other malware proliferation. In particular, the latest anti-virus software can defend users from spyware, adware, fraud tools, dialers, malicious LSPs, worms, trojan horses, rootkits, backdoors, keyloggers, ransomware, browser highjackers, and mischievous browser helper objects. Also, some products include protection from several computer threats like malicious and infected botnet DDoS attacks, APT (advanced persistent threat), social engineering techniques, online banking attacks, online identity, fishing and scam attacks, spam, and malicious URLs. Anti-virus identification methodsSome solid theoretical outcome in the computer virus study is Fredrick B. He said that no algorithm can find every possible virus perfectly. However, by applying distinct defense layers, a good rate of detection might be achieved. There are many techniques that antivirus engines can apply for identifying malware: 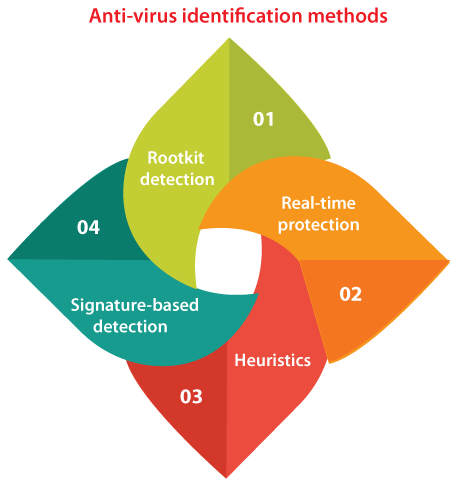
The anti-virus engine can decide if the program is mischievous or not relying on the operation logged. If not, the program is run within the real environment. This method has shown to be quite impressive, given its slowness and heaviness, it's rarely applied in several solutions of the end-user antivirus. Signature-based detectionClassical anti-virus software heavily depends upon signatures for identifying malware. When a sample of malware substantially comes into the antivirus firm's hands, it is investigated by dynamic analysis systems or malware researchers. Then, a proper file signature is derived and included in the signature database of an anti-virus software once it is confirmed to be malware. However, the signature-based method can effectively include malware outbreaks, many malware authors have attempted to stay ahead of a step of application by writing "polymorphic", "oligomorphic", and more newly "metamorphic" viruses, that encrypt segments of themselves or change themselves as a disguised method, to not the same virus signature within the dictionary. HeuristicsSeveral viruses begin as one infection and from either refinements or mutation by other attackers, can develop into many slightly distinct strains, known as variants. Generic detection defines the detection and deletion of multiple threats with one virus definition. For instance, the Vundo Trojan has many family members, relying on the anti-virus classification of the vendor. Symantec divides the Vundo family members into two different categories: Trojan.Vundo.B and Trojan.Vundo. While it might be beneficial to detect a particular virus, it could be faster to find a virus family from a generic signature or an inexact match to a previous signature. The researchers of the virus detect common areas that every virus of a family uniquely shares and can establish one generic signature. Often, these signatures include non-contiguous code with wildcard characters in which differences lie. The wildcards permit the scanner to find viruses even if they are protected with meaningless and extra code. A detection that applies this method is called "heuristic detection". Rootkit detectionAn antivirus application can attempt for scanning rootkits. The rootkits are a kind of malware established for gaining administrative-level control on a computer device without being found. Rootkits can modify how the OS functions and, in a few cases can tamper with an antivirus program and consider it ineffective. Also, rootkits are hard to remove, in a few cases needing a full re-installation of the OS. Real-time protectionAuto-protect, resident shield, background guard, on-access scanning, real-time protection, and other synonyms define the automatic protection given by most anti-spyware, antivirus, and other anti-malware functions. It monitors computer devices for malicious activities like adware, spyware, computer viruses, and other mischievous objects. Real-time protection finds threats in files and scans applications in real time because they are downloaded on the device. Related Issues of Antivirus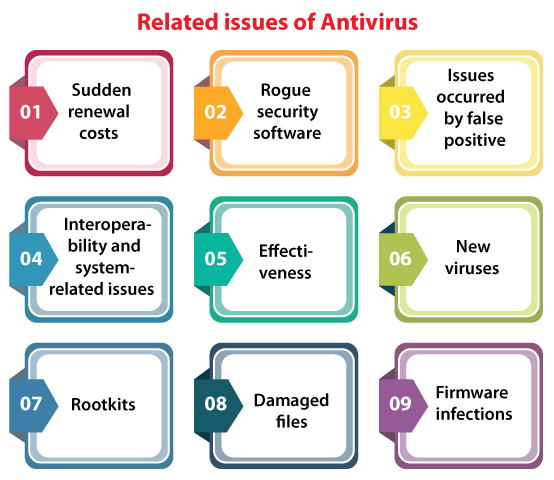
Sudden renewal costsA few commercial end-user license agreements of antivirus software contain a section that the subscription will automatically be renewed and the credit card of the purchaser billed automatically, during the renewal time without clear approval. Rogue security softwareA few apparent programs of antivirus are malware masquerading as genuine software like Mac Defender, MS Antivirus, and WinFixer. Issues occurred by false positiveA "false alarm" or "false positive" is when an anti-virus application recognizes a non-mischievous file as malware. It can lead to some serious problems when it happens. Some Serious false positive examples are listed and explained below:
Interoperability and system-related issuesRunning more than one antivirus program simultaneously can create conflicts and degrade performance. However, various companies (including Microsoft and G Data Software) have established applications that can execute more than one engine concurrently using a concept known as multiscanning. Sometimes, it is essential to disable antivirus protection temporarily if installing big updates like updated graphics card drivers or Windows Service packs. Running antivirus protection may completely or partially prevent major update installation. Antivirus applications can lead to some problems at the installation time of an OS upgrade. EffectivenessDecember 2007 studies represented that the effectiveness of an anti-virus application had diminished in the previous year, specifically against zero-day or unknown attacks. The c't computer magazine detected that detection rates for the attacks had decreased from 40-50% in 2006 to 20-30% in 2007. The only exception at that time was the NOD32 antivirus, which handled 68% of the detection rate. The issue is magnified by the virus author's changing intent. It was obvious if a virus infection was available a few years ago. At that time, viruses were specified by amateurs and destructive pop-ups or behavior. Often, modern viruses are specified by professionals and financed by some criminal organizations. New virusesAnti-virus applications are not always efficient against fresh viruses, even those that applied non-signature-based techniques that should find fresh viruses. The cause for it is that the virus designers inspect their new viruses on the big antivirus software to make sure that they aren't found before publishing them into the wild. A few new viruses, specifically ransomware, apply polymorphic code for avoiding disclosure by virus scanners. A virus, i.e., proof of concept had used the GPU (Graphics Processing Unit) for avoiding disclosure from antivirus applications. Its potential success involves bypassing the Central Processing Unit to make it much more solid for security researchers to evaluate the inner implementation of such malware. RootkitsIdentifying rootkits is a big challenge for all anti-virus applications rootkits have complete administrative access to the system and are unseen to users and hidden from the running process lists in the task manager. Rootkits can change the inner implementations of the OS and interfere with antivirus applications. Damaged filesAn antivirus application will attempt to delete the virus code through the file at the time of disinfection, but it's not always able for restoring that file to an undamaged state if a file is infected by a system virus. Damaged files can be only restored from previous shadow and backup copies (it is also accurate for ransomware), installed software that's damaged needs reinstallation in such situations. Firmware infectionsIn the computer, a writeable firmware could be infected by mischievous code. It is a major concern, as any infected BIOS can need the real BIOS chip to be substituted to make sure the mischievous code is removed completely. Antivirus application is not efficient at protecting motherboard BIOS and the firmware from infection. Security researchers found that USB devices include writeable firmware that can be changed with mischievous code ("BadUSB") in 2014, which antivirus applications can't prevent or detect. The mischievous code can execute undetected on the system and can even infect the OS before booting up. Antivirus applications for Ubuntu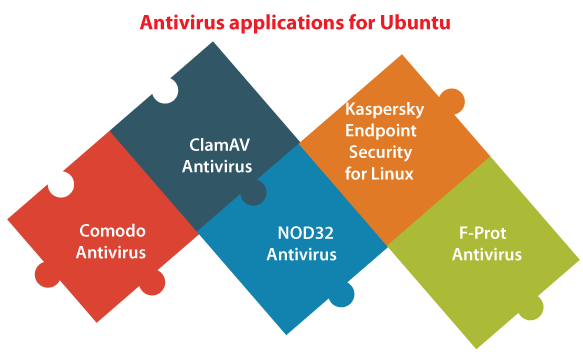
Comodo AntivirusComodo antivirus is also known as CAVL (Comodo Antivirus for Linux) provides similar virus protection as Windows software along with extra features of a completely anti-spam configured system. Features of Comodo
ClamAV AntivirusIt is an open-source antivirus engine used in a range of situations including endpoint security, web scanning, and email scanning. It offers several utilities including a scalable and flexible multi-threaded daemon, an advanced tool for database updates automatically, and a command-line scanner. Features of ClamAV
NOD32 AntivirusProtect our workstation of Linux from threats designed for Linux and every cross-platform malware that can pass on to other Apple or Windows computers within the network. For Linux desktop, ESET NOD32 antivirus is a completely fledged solution of antivirus that plays a necessary role in protecting our online identity. Features of NOD32
Kaspersky Endpoint Security for LinuxIt offers corporate networks executing Unix-based OSes on their end machines along with centralized protection from every kind of malware and possibly dangerous programs. It comes from a product family that is based on a uniform set of the best anti-malware and other technologies, the innovative fresh antivirus engine of Kaspersky Lab applies the architecture of cutting-edge components for increasing its stability and performance, offering reliable protection that is easy to manage and control. Features of Kaspersky 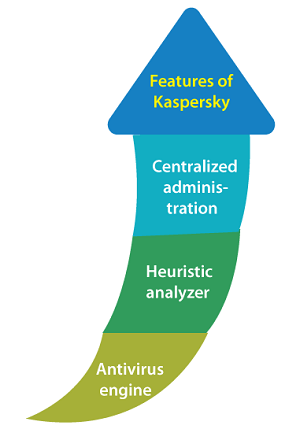
F-PROT AntivirusF-PROT antivirus establishes on the reliability history of the product, is easy to use, and provides a robust yet affordable solution of antivirus. For Linux workstations, F-PROT anti-virus is easy to use, efficient, and fast. It can protect Linux workstations from the increasing worms, virus threats, and other malware by disinfecting and detecting or removing mischievous programs. Several unknown threats can be found with the heuristic technology of F-PROT, hence offering the strongest defense present and being the best solution for our desktops and laptops.
Next TopicUbuntu Image Editor
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










