Ubuntu VNC ServerIntroduction to VNC ServerVNC stands for Virtual Network Computing, and it is a graphical desktop-sharing system that utilizes the Remote Frame Buffer Protocol (in short RFB) to control other computers remotely. It transmits the mouse and keyboard input from one computer to the other, delivering the graphical-screen updates on a network. VNC is a platform-independent system: there are servers and clients for several GUI-based OSes and Java. More than one client may connect to any VNC server. Famous uses for this technology are accessing files and remote technical support on the work computer of one from the home computer of one or vice versa. Originally, VNC was integrated at the Olivetti & Oracle Research Lab, the United Kingdom, in Cambridge. The real VNC source code and several latest derivations are open source upon the GNU General Public License. Several VNCs are available that provide their particular functionality. For example, some are used for Microsoft Windows, providing file transfer, etc. Several are compatible (without added aspects) with VNC that a viewer of a flavor can link with another server; others are VNC code-based but not suitable with classic VNC. RFB and VNC are RealVNC Ltd. registered trademarks in the United States and a few other countries. History of VNC ServerThe Olivetti and Oracle Research Lab (in short ORL) in the UK at Cambridge integrated VNC when Olivetti and Oracle Corporation acquired the lab. AT&T inherited the lab in 1999 and closed down the research efforts of the lab in 2002.
Several development team members (including Hopper, Weatherall, Harter, and Richardson) formed RealVNC to continue operating on commercial VNC software and open source upon that name following the ORL closure in 2002. The original source code of GPLed has fed into many other VNC versions. This forking hasn't led to compatibility issues because the RFB protocol is developed to be extensible. VNC servers and clients negotiate their abilities with handshaking to apply the most accurate options supported by both ends. RealVNC Ltd claims the "VNC" title as a registered trademark in the US and other countries as of 2013. The "Virtual Network Computing" title originated with the work of ORL on a thin client known as VideoTile, which used the RFB protocol. The VideoTile included an LCD display with a fast ATM connection and pen input to the network. Commonly, a network computer was used as any synonym for a thin client at the time; VNC is originally a software-only network computer. Operations of VNC Server
On the server, a viewer can connect to any port (5900 is the default port) in the general method of operation. Alternatively, relying on the implementation, any browser can connect to any server (5800 is the default port). A server can connect to any viewer in the listening mode on the 5500 port. One benefit of listening mode is that a server site doesn't have to construct its firewall to permit access on the 5900 port (or 5800); the responsibilities are on the viewer, which is helpful if that server site has no system proficiency, and the viewer user is more experienced. The server transfers the small framebuffer rectangles to the client. The VNC protocol can apply a lot of bandwidth in its easiest form, so many methods have been created to decrease communication overhead. For instance, there are many encodings (methods to decide the most efficient way to send these rectangles). The VNC protocol permits the server and client to communicate which encoding method they will use. The easiest encoding, supported by every server and client, is raw encoding, which transfers pixel data in the left-to-right side scanline order, and only transfers rectangles that modify after the actual full screen has been sent. This encoding operates very well if just a small screen portion modifies from one frame to the other.
Xvnc is a Unix VNC server based on a classical X server. For applications, Xvnc occurs (that shows client Windows), and it is a VNC server for remote VNC users. Applications can show themselves on Xvnc as when it was a general X display. However, they will occur on a connected VNC viewer instead of a physical screen. A machine (that might be a network server or workstation) with the mouse, keyboard, and screen can alternatively be set up to restart and execute the VNC server as a daemon or service, then, the mouse, keyboard, and screen can be deleted, and the machine saved in an isolated location. The display is not essentially the similar display seen on the server by a user that is served by a VNC. On Linux/Unix computers that support more than one simultaneous session of X11, VNC may be set up to serve a specific existing session of X11 or to begin one of its own. Also, it is possible to execute more than one VNC session from a similar computer. The VNC session is always the latest user session which is served on Microsoft Windows. Commonly, users set up VNC as any cross-platform remote desktop system. For instance, for macOS X, Apple Remote Desktop interacts with VNC, and it will connect to the current desktop of a Unix user if it's served with x11vnc or isolates the X11 session if anyone is served with TightVNC. TightVNC will link to a macOS X session, which is served by Apple Remote Desktop if a VNC option is activated, or to a VNC server executing on Microsoft Windows from Unix. RealVNC released a Wayland developer preview in July 2014. Security of VNC ServerRFB is, by default, not a secure protocol. Cracking can prove successful when both encoded password and encryption key are sniffed through a network while passwords are not transferred in plain text. For this reason, it's suggested that a password of at least 8 characters should be used. Besides, there is an 8-character limit on a few VNC versions; the other characters are deleted, and the added string is compared with the password if a password is transferred exceeding 8 characters. UltraVNC supports the utilization of an open-source encryption plug-in that can encrypt the whole VNC session, including data transfer and password authentication. Also, it permits authentication to be implemented based on Active Directory and NTLM user accounts. Although, the use of these encryption plugins makes it unsuitable with other programs of VNC. RealVNC provides high-quality AES encryption as a part of its financial package with Active Directory integration.
An extra security concern is to inspect whether the release needs authorization from any remote computer owner before anyone takes control of their machine for VNC use. It will ignore the situation in which the computer accessed owner realizes that there's someone in control of their machine without older notice. Basic Security Options of VNC ServerThe most essential thing during set up is just to let the correct people access our desktop. To do it, the safest way is usually to have anyone sitting at the desktop determining who gets to use it, but that is not always practical. For example, if we wish to log in to our computer from somewhere else. If you wish to confirm all connections manually, we should look at the following options:
The above two options will provide us with the most security. Request access all time will ensure that no one can connect without us noticing, and view only-access will ensure that they can not modify anything without asking us to do it for them. If we wish to access our desktop when no one is sitting at it, the following options will be more helpful:
The above three options should provide us with a secure setup, as long as they are using port-forwarding. Just permitting local connections means only people using user accounts on our computer can access our desktop. Beginning the server in "once" mode defines that people using user accounts on our computer would need to log in to our desktop between the period we start our VNC server and the period we connect from our VNC client. Creating a password defines that if someone did attempt to connect in that brief period, they would not be able to get inside before we noticed and disabled the server. Important: We must create a password if we wish to utilize the in-built client within Mac OS X. What is Vino?It is the default VNC server to share our previous desktop with others in Ubuntu. To set up vino from in GNOME, we need to visit System > Preferences > Remote Desktop.
What is x11vnc?It is a VNC server that's not dependent on any specific graphical environment. It also offers use in a minimal environment because it has a tk/tcl-based GUI. It can be begun while our system is still displaying a login screen. It's useful to ensure we have first deleted any other program of VNC so that they do not interfere with this server. Here are some settings that will be basic for adjusting depending on our environment:
What is Krfb?In Kubuntu, it is the default VNC server. Because it is highly developed with KDE, it is difficult to run it in other environments. To set up krfb, we need to visit System Settings > Sharing > Desktop Sharing > Configure.
Invitations Krfb enables us to make "invitations" or single passwords deactivated after one use or an hour. There is also a convenient way of providing people one-time access to a device, but it only gives limited security. For instance, if we transfer someone an invitation by instant messaging or email, an attacker can read our invitation message because it is transferred over the Internet. Invitations can be helpful when we wish to enable other people to view our desktop, but we still have to pursue the basic precautions if letting other people view our desktop. TightvncserveTightvnc creates a fully new desktop, not linked to any real screen, whereas almost all VNC servers share our desktop. It makes it much less helpful for a few things (such as remote help) but much more helpful for others (such as making a public area for collaboration). We might have to uncomment the $fontpath lines within the /etc/vnc.conf directory if tightvncserver would not start. Tightvnc is developed to be executed from the command line like x11vnc. To start it, enter: It will tell tightvnc for listening VNC connections on the 5901 port on the internet from anywhere. Without -nolisten tcp, tightvnc will listen for a distinct connection type (X11 rather than VNC), which is not very useful. The unusual design of tightvnc means that it cannot make a remote desktop over the standard VNC port if we have a normal desktop executing on our computer.
TightVNCOriginally, TightVNC was based on the VLC 4 TightVNC branch. It's actively maintained and stable, being around since 2009 and added in the most famous distros. It provides its support to composite window managers without needing a fallback mode, like with the GNOME shell. Also, it, by default, applies TLS encryption if used with the TightVNC viewer. Same applications
Installing VNC Server in UbuntuIn this section, we will explain how we can install and configure VNC on our Ubuntu system. Updating the systemWe need to update our system repositories by running the following command in the terminal window: 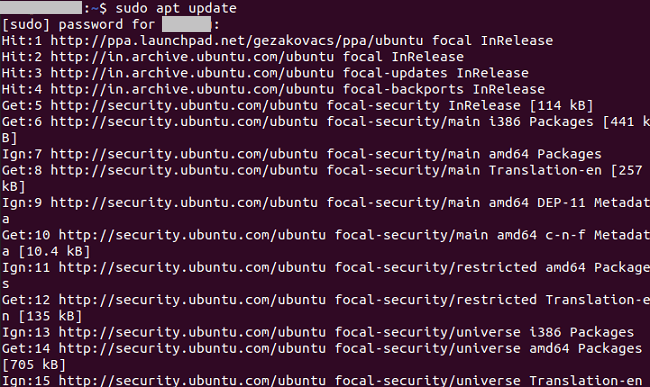
We will get the graphical interface in the next step. Installing the Xfce desktop environmentWe might know that the servers of Ubuntu are managed by the command line, and they don't have a built-in desktop environment. We can skip this step if we are utilizing the Ubuntu desktop version. We will find a range of desktop environments inside the Ubuntu repository. We will install Xfce in this article, which is a robust and lightweight desktop environment, and good to use on any remote server: 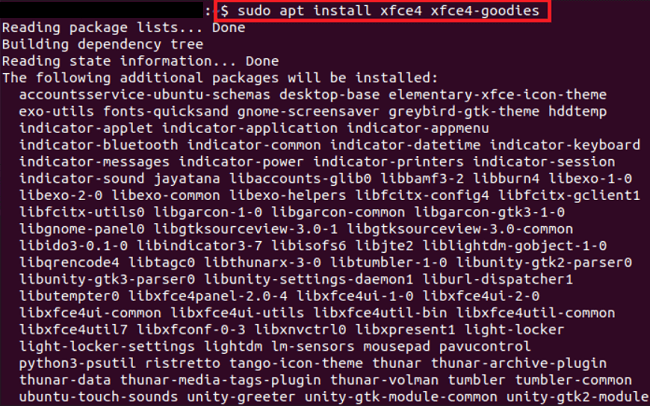
We need to enter "Y" to allow the installation process of Xfce to continue. After that, a prompt will occur on the command-line screen requesting us to setup lightdm: 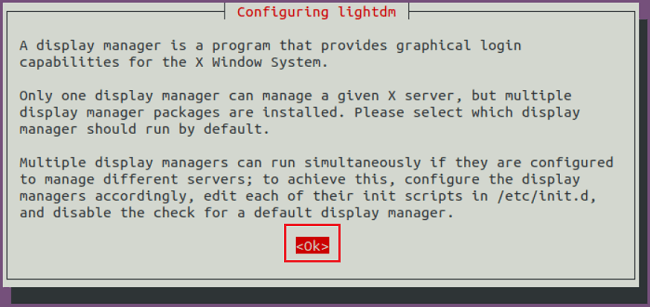
We can choose between lightdm and gdm3 as the default display manager.
Next TopicUnable to Locate Package Ubuntu
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










