Caesar Cipher TechniqueThe Caesar cipher is the simplest and oldest method of cryptography. The Caesar cipher method is based on a mono-alphabetic cipher and is also called a shift cipher or additive cipher. Julius Caesar used the shift cipher (additive cipher) technique to communicate with his officers. For this reason, the shift cipher technique is called the Caesar cipher. The Caesar cipher is a kind of replacement (substitution) cipher, where all letter of plain text is replaced by another letter. Let's take an example to understand the Caesar cipher, suppose we are shifting with 1, then A will be replaced by B, B will be replaced by C, C will be replaced by D, D will be replaced by C, and this process continues until the entire plain text is finished. Caesar ciphers is a weak method of cryptography. It can be easily hacked. It means the message encrypted by this method can be easily decrypted. Plaintext: It is a simple message written by the user. Ciphertext: It is an encrypted message after applying some technique. The formula of encryption is: En (x) = (x + n) mod 26 The formula of decryption is: Dn (x) = (xi - n) mod 26 If any case (Dn) value becomes negative (-ve), in this case, we will add 26 in the negative value. Where, E denotes the encryption Note: "i" denotes the offset of the ith number of the letters, as shown in the table below.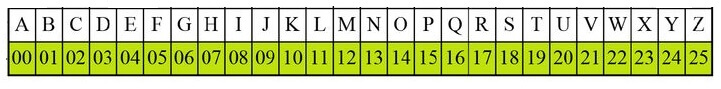
Example: 1 Use the Caesar cipher to encrypt and decrypt the message "JAVATPOINT," and the key (shift) value of this message is 3. Encryption We apply encryption formulas by character, based on alphabetical order. The formula of encryption is: En (x) = (x + n) mod 26
The encrypted message is "MDYDWSRLQW". Note that the Caesar cipher is monoalphabetic, so the same plaintext letters are encrypted as the same letters. For example, "JAVATPOINT" has "A", encrypted by "D". Decryption We apply decryption formulas by character, based on alphabetical order. The formula of decryption is: Dn (x) = (xi - n) mod 26 If any case (Dn) value becomes negative (-ve), in this case, we will add 26 in the negative value.
The decrypted message is "JAVATPOINT". Example: 2 Use the Caesar cipher to encrypt and decrypt the message "HELLO," and the key (shift) value of this message is 15. Encryption We apply encryption formulas by character, based on alphabetical order. The formula of encryption is: En (x) = (x + n) mod 26
Note that the Caesar cipher is monoalphabetic, so the same plaintext letters are encrypted as the same letters. Like, "HELLO" has "L", encrypted by "A".The encrypted message of this plain text is "WTAAD". Decryption We apply decryption formulas by character, based on alphabetical order. The formula of decryption is: Dn (x) = (xi - n) mod 26
The decrypted message is "HELLO". Note: If any case (Dn) value becomes negative (-ve), in this case, we will add 26 in the negative value. Like, the third letter of the ciphertext.Dn = (00 - 15) mod 26 The value of dn is negative, so 26 will be added to it. = -15 + 26 Advantages of Caesar cipherIts benefits are as follows: -
Disadvantages of Caesar cipherIts disadvantages are as follows: -
ProgramC program for the encryption: C program for the decryption
Next TopicProgramming Language
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









