Vault DownloadVault IntroductionVault can be defined as a tool to access secrets. The secrets can be anything that we wish to tightly manage access to, like certificates, passwords, or API keys. Vault facilitates the unified interface for a secret while facilitating recording the detailed audit log and tight access management. Any modern system needs access to the secret's multitude: API keys to external services, database credentials, credentials for the architecture communication (service-oriented), etc. Adding on the detailed audit log, secure storage, and key rolling is impossible without any custom solution. Vault features:Various vault key features are discussed as follows: 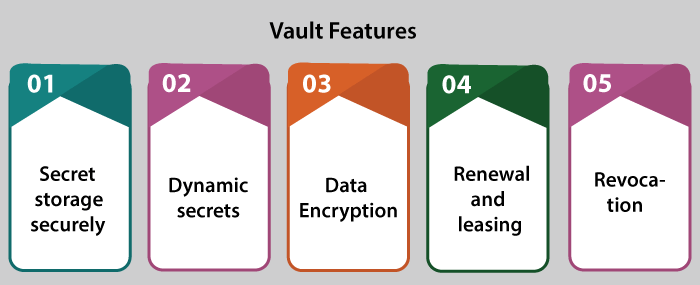
1. Secret Storage Securely: Arbitrary value/key secrets are stored within the Vault. Vault can encrypt secrets before writing them for persistent storage. Hence, gaining the access to any raw storage is not enough for accessing our secrets. Vault can be written to Consul, disk, and other. 2. Dynamic Secrets: The vault tool can produce on-demand secrets for a few systems, like SQL or AWS databases. For example, if an application requires accessing the S3 bucket, it will ask Vault for many credentials, and produces the AWS key pair along with some valid on-demand permissions. After making the dynamic secrets, Vault will revoke them automatically. 3. Data Encryption: Vault decrypts and encrypts information without storing it. It permits security groups to define the parameters for encryption. It also permits developers for storing encrypted data inside a location, such as SQL without designing their methods of encryption. 4. Renewal and Leasing: Every secret Within Vault includes the lease associated along with them. Automatically, Vault will cancel that secret at the lease's end. Clients can renew the lease by renewing built-in APIs 5. Revocation: Vault includes built-in support for various secret revocations. It can cascade not only a single secret, but a tree of secrets. For example, every secret read via some specific users or every secret of the particular type. The revocation assists within the key rolling and locking-down the systems. It can also be within an intrusion case. Install VaultWe can install Vault by using various approaches:
Linux package installation is efficient and easy. If we deploy or develop on other platforms, the precompiled binary usage will be efficient and easy. Linux package installationIt signs and builds official packages from Amazon Linux, Fedora RHEL, Debian, Ubuntu, and another distribution. Precompiled binary usageDownload an appropriate package for our system for installing the precompiled binary. Currently, Vault is packaged like any zip file. Unzip the zip file into a directory after it is downloaded. The Vault binary is necessary to execute vault (for Windows vault.exe). No other files will be required to execute Vault. On our system, copy the binary where we want. If we want to access it through a command-line, ensure to position it anywhere on our PATH. Install through sourceWe will need GO configured and installed properly to compile through the source (including the variable set of GOPATH environment). We can also include git copy in our PATH. Clone a Vault repository through GitHub into out GOPATH Bootstrap this project. It will compile and download tools and libraries required for compiling Vault. $ make bootstrap Create vault for our latest system and also put the binary within ./bin/ (relevant to git checkout). The make dev destination is a shortcut that is used to create vault for our local created environment only no cross-compiled destinations). Installation VerificationsExecute vault -h command on our system for verifying vault is installed properly. We must check-out the help result. If we are running it through a command line, ensure that it is on our PATH. We may get any error that Vault has not found.
Next TopicDefine Acculturation
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









