What is DevSecOps?DevSecOps is a strategy for incorporating safety protocols into the DevOps procedure. It fosters and encourages collaboration among security staff and launch technicians based on the 'Security as Code' ideology. Considering the ever-increasing vulnerabilities to software programs, DevSecOps has increased in popularity and significance. It is also identified as "Development Security Operation." DevSecOps is a recursive system that integrates protection into your product pipeline. It extensively integrates safety into the majority of the Development Operation (DevOps) methodology. It is crucial for software development teams to evaluate for potential threats and weaknesses. Until the alternative can be implemented, security professionals must tackle problems. This incremental methodology guarantees that security flaws are highlighted. As a current and innovative restraint, DevSecOps may take some chance to accumulate universal attention and assimilation. Late in the manufacturing process, a substantial set of security procedures are conducted. This postponement can have severe consequences for businesses and their product lines. Safety is typically among the last characteristics to be considered during the development phase. When safety problems occur near release, if protection is kept after the development pipeline, you will discover yourself back at the beginning of lengthy development processes. Working of DevSecOps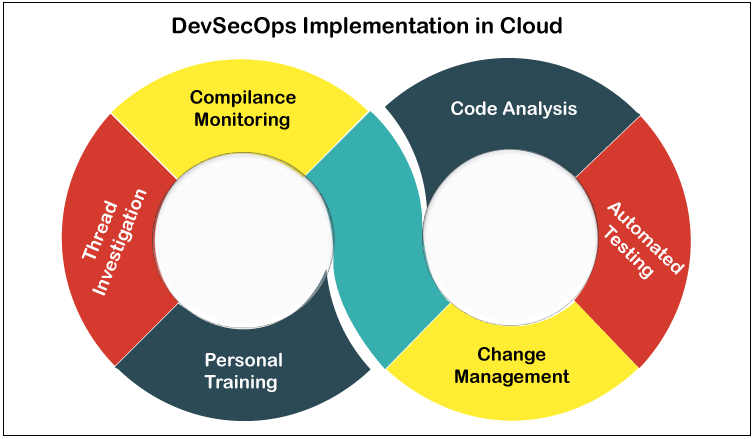
The DevSecOps methodology necessitates more than just collaboration between innovation and activities team members. Security people must also be involved early in the generation procedure to improve total software security from beginning to end. You must consider facilities and vulnerability scanning from the start. Companies can better follow instructions and make sure client and end-user satisfaction by implementing this procedure. IT must incorporate security throughout the life cycle of your application areas. By incorporating security into your procedures, you can benefit from the sensitivity and endurance of a Development Operation (DevOps) approach. The following are the significant regions of security software evaluation that are being used:
When software applications are operating; alternatives can monitor them to guarantee that no malevolent steps are needed. Scanners like Burb Intruder and OWASP Zap mechanization will evaluate and analyze apps to maintain that they are not performing actions that end users may interpret as suspicious.
Software tools, including the Microsoft Azure Advisor tool for cloud-based facilities, can be established to maintain that the framework is configured correctly and safe for use in particular contexts. Many test automation tools are built to work in a particular environment, including a smartphone or web-based atmosphere. It is possible to make sure that technology is designed to these correct specifications during the design phase.
Code analysis tools can help Development Operations cybersecurity capabilities by instantly inspecting scripts and evaluating critical and recognized vulnerabilities. It can be helpful data for software development teams as they operate, as they will be able to address problems before they are captured in quality management. It can also aid in the development of improving cognitive behaviors. Development Security Operation (DevSecOps) Implementation Process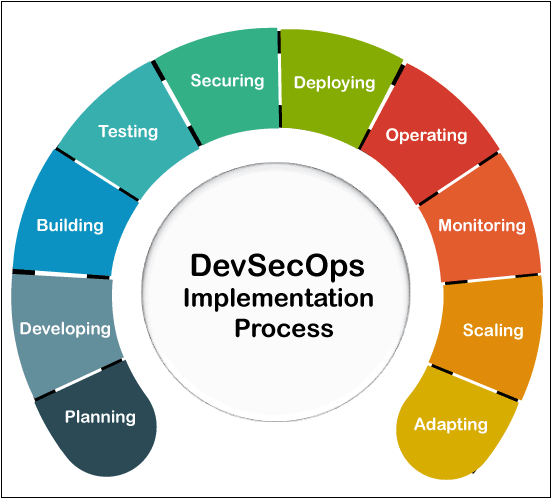
Each group apparently in DevSecOps must relate to the achievement of the team. It includes the following aspects-
Programmers play an essential role in the DevSecOps procedure. Developers must be willing to collaborate with procurement and security people. The involvement of these groups from the beginning of the design and development phase will promote a protected DevOps transition and make applications extra safe. It is critical to prepare programmers for safety industry standards if they are to be successful. Businesses can augment this coaching by employing developers with DevSecOps knowledge to assist the members of the league. Corporations must create a culture in which programmers understand that creating security is a joint effort among them and security people. System administrators can only make recommendations about security protocols. It is the moral obligation of programmers to put them into action.
The operations squad's participation is comparable to that of the design team. Security professionals and working groups must work together. They are in charge of performing vulnerability scans on network and communication setups. To ensure the success of DevSecOps, security professionals will also require to coach procurement teams on security procedures. The processes and security companies will then collaborate to configure both manual and automated safety checks to determine network configuration adherence.
DevSecOps is an alteration for security staff almost as much as it is for innovation and activities groups. Security teams must start increasing their participation while working alongside growth and processes groups. Professionals of protection should begin with the idea of 'shifting left.' Working with production and procedures team members to migrate security reviews and technical regulations earlier in the software development process. This procedure of moving left is critical for reducing the likelihood of future security concerns. Security policies are usually regarded as a time-consuming and challenging process by growth and functions teams. As a result, the security staff's responsibility applies beyond implementing safety tests to implicating and mentoring other groups. Security Solutions in DevSecOps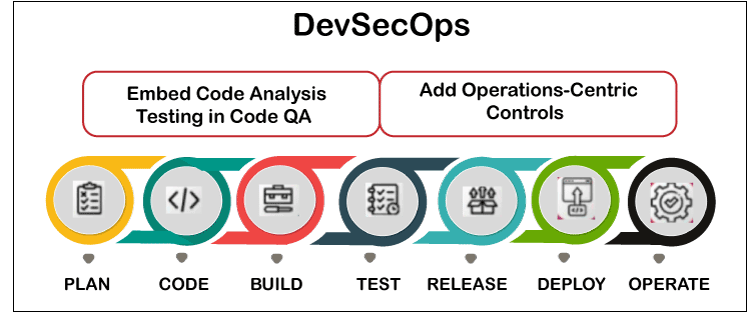
DevSecOps incorporates protection into the implementation phase, but it cannot be done quickly or without scheduling. Incorporate it into the design and construction phase. Businesses can work to improve their business processes by implementing some of the industry's leading practices.
It may appear insignificant, but bringing together all necessary groups can make a massive difference in your DevSecOps strategy. The formal assessment of giving off recently released incarnations to Quality Assurance (QA) teams is well known to design units. This separated action is the rule in corporations where each team operates in its silo.
Developers are nearly solely accountable for the success of the script they create. System failures cause many unpatched vulnerabilities and difficulties. However, businesses pay less attention to their programmers' training and professional advancement when it comes to managing programming codes. Teaching developers on most acceptable coding practices can explicitly contribute to increased code coverage. Good code performance gives fewer opportunities for security flaws. Elevated source code will also make it easier for security professionals to evaluate and remediate any security issues.
Nowadays, very few organizations implement all of their scripts in-house. Each implementation is more likely to be developed on a substantial quantity of third-party, fully accessible code. Raising the dangers, many businesses utilize third-party technology elements and open-source technology in their application areas rather than designing them from the ground up. Coders infrequently can consider script or paperwork due to the high stress of meeting customers' needs.
DevOps groups commonly use continuous Integration (CI) techniques to optimize sections of the development phase, including evaluating and establishing. These are periodic activities that the groups must perform with each new edition. Adding security measures to Project Collaboration techniques and systems means that security professionals diagnose problems before verifying CD (Continuous Delivery) designs. CI also decreases the amount of time expended on each incarnation. For instance, utilizing SAST (static application security testing) on traditional designs will help you make sure that you're only checking for situations or areas of value in the adjustments to your script that were engaged that day.
Simplistic code is simpler to comprehend and maintain. Programmers will find it a lot easier to troubleshoot the code if it is straightforward and easy to understand. Code that is neat and tidy will also result in fewer security concerns. If the source code is easy, developers will frequently interact and operate over each other's scripts.
The principle of 'Security as Code' is incorporating security standards into the current Development Operations pipeline. The dynamic analysis of script is among the essential aspects that this principle necessitates. In comparison to scanning the overall coding standard, security professionals can concentrate on testing or change the script.
Your implementation should be tested regularly. It should also be subjected to more stringent testing, like mitigating denial of service (DOS) attacks. There may be flaws in a remedy that become apparent only when it is damaged. These are still legitimate issues that the project manager may encounter. Malware activities on companies are becoming more common. These threats may target any element of a client's company visible from elsewhere in the channel. You can protect your apps via diverse circumstances by checking them under, especially stressful conditions. Advantages of DevSecOps strategySecurity measures baked into the design phase instead of provided as a "layer on top" enable Development Operations and security professionals to demonstrate the energy of agile practices as a group without jeopardizing the aim of developing cryptographic codes. According to a 2017 EMA study, the two leading advantages of security operations (SecOps) are enhanced Return on investment (ROI) on current security facilities and increased productivity improvements across security and the remainder of IT. One other tangible advantage identified in the research was the capacity to utilize cloud solutions fully. For instance, Companies that deliver services in the AWS (Amazon Web Services) cloud, advantages from enhanced preventive and reactive security protocols as part of AWS continuous delivery and enlistment prototype. While more businesses focus on cloud services to retain business running, safety efforts autonomous of AWS's are critical to reduce unnecessary breakdowns. The security measures built into DevSecOps have numerous additional benefits. These are some examples:
DevOps vs. DevSecOpsHere, we have the comparison table between DevOps and DevSecOps that is given below-
Tools of Development Security Operations (DevSecOps)We've compiled an index of some of the best DevSecOps toolkits that businesses can assimilate into their DevOps piping system to ensure safety is controlled constantly throughout the development process. These tools are- 1. Codacy
Codacy provides development groups with a high-quality mechanization and optimization remedy, allowing them to transfer as far left as possible in the design process, introducing potential problems as soon as possible. Their static code analysis platform helps designers instantly identify and resolve security problems, redundancy, difficulty, classic infringements, and connectivity gaps with each dedicated and drag proposal, explicitly from their Git workspace. Features of Codacy
You can download this tool by clicking on the below link- 2. Acunetix
Acunetix provides an All-in-One internet security scanning to assist programmers in finding vulnerabilities as early as possible. Acunetix's mission is to assist corporations with a significant online presence in protecting their web assets susceptible to malware by providing exceptional techniques that help developers detect more difficulties and rapidly resolve them. The alternative is simple to implement and allows for centralized control, computerization, and assimilation. Acunetix is a better solution and one of the industry's most established solutions because it concentrates on internet security and is associated with highly scanning, negligible false positives, easiness of use, distinctive techniques, and SDLC implementation. Features of Acunetix
You can download this tool by clicking on the below link- 3. SonarQube
SonarSource's open software project also aims to assist programmers via computerization. SonarQube is a code coverage tool that automatically detects errors, security flaws, and code stinks in your source code. It incorporates the native frameworks of design teams to offer continuous code evaluation across several project divisions and pull requests. SonarQube endorses approximately 27 programming languages and enables reliable code checking, allowing small development teams and businesses relatable to identify problem and defects weaknesses in their applications, preventing unspecified actions from affecting end users. Features of SonarQube
You can download this tool by clicking on the below link- 4. Gitlab
GitLab is a web-based Development Operations model that supports an entire CI/CD toolkit in a separate application. It promotes collaboration among Growth, Safety, and Operations teams, allowing them to achieve faster and recognize security issues without slowing or stopping the CI/CD pipeline by reducing toolchain intricacy. GitLab, in addition to being titled a CI member, provides the full kit to assist organizations in reducing their Development Operations processing time by merging silos, phases and facilitating a cohesive workload that decreases and simplifies events that were previously separate, such as application security and CI/CD. Features of Gitlab
You can download this tool by clicking on the below link- 5. Aqua Security
Aqua security saves the day by securing jars throughout the Development Security Operations pipeline. Aqua's cloud-native threat protection gives users total control over container-based conditions at level, with strict debugging security measures and intrusion detection abilities. The framework offers customers an API that allows for simple integration and computerization. The Aqua package Security Platform provides entire SDLC (software development life cycle) controls for safeguarding intermodal programs running on-premises or in the data center and Linux or Windows. The framework is compatible with a wide range of improvisation environments. Features of Aqua Security
You can download this tool by clicking on the below link-
Next Topicnpm clear cache
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









