What is Metasploit?It is an open-source project which offers the public resources to develop codes and research security vulnerabilities. It permits the network administrators for breaking their network to recognize security threats and also document which vulnerability requires to be defined first. It is a type of project that facilitates Pen (Penetration) testing software. Also, it offers tools to automate the comparison of a vulnerability of a program and its patched (repaired) version. It also offers advanced evasion and anti-forensic tools. A few of these tools are created into the framework of Metasploit. Let's discuss some key points.
The Metasploit Project was inherited in 2009 by the computer security organization Rapid7. Metasploit Pro and Metasploit Express are the Metasploit Framework's open core version with additional features. Open core is a way to deliver products that associate proprietary and open-source software. Rapid7 continues to developing Metasploit in association with an open-source community. Metasploit FrameworkOne of the most effective creations of the Metasploit Project is the Metasploit Framework. Metasploit Framework is a software environment to develop, test, and execute exploits. It could be used for creating tools for security testing, exploiting modules, and as a pen-testing system. Originally, it was developed in 2003 as a movable network tool by HD Moore. This framework is a very strong tool. It can be applied by ethical hackers and cybercriminals for probing systematic susceptibilities on servers and networks. Because it is an open-source framework, it can be easily used and customized with various operating systems. The pen testing group can apply custom code or ready-made and address it in a network for probing for weak spots with Metasploit. Once the flaws are documented and identified as another threat hunting flavor, the information could be used for prioritizing solutions and addressing systemic weaknesses. Metasploit Brief HistoryIn 2003, the Metasploit Project was attempted by HD Moore to use as any Perl-based movable network tool along with assistance from Matt Millar core developer. It was completely transformed into Ruby in 2007. The license was inherited in 2009 by Rapid7, in which it remains the same as a segment of the Boston-based organization's repertoire of the IDS signature evolution and targeted evasion tools, anti-forensic, fuzzing, and remote exploit.
Who can use Metasploit?Because of its wide range of open-source availability and applications, Metasploit can be used by almost everyone from the growing area of DevSecOps pros to many hackers. It is useful to those who require a reliable and easy-to-install tool. It can complete the task irrelevant of which language or platform is used. This software is widely available and famous with various hackers. It reinforces the requirements for many security professionals for becoming familiar with this framework even when they do not use it. Now, Metasploit contains 1677+ exploits arranged on 25 platforms, such as Cisco, Java, Python, PHP, Android, and others. Also, the framework carries approximately 500 payloads. A few of these payloads are below: 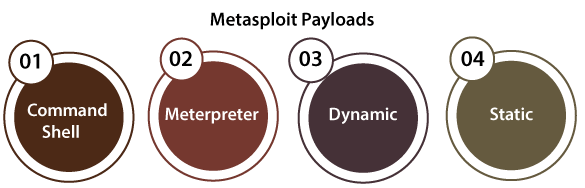
Modules of MetasploitMetasploit offers us some modules for:
Commands of MetasploitHere are a few common commands of the Metasploit console we must know about. This Metasploit console is also referred to as the msfconsole which appears to be the batch file name that begins up the program. Commands we must know about include:
msfupdate is another essential command. Msfupdate is not just a command that we run inside the console, but the external program created inside the Metasploit Framework. This command can also be defined as a batch file positioned within the Metasploit Framework/bin folder which can download and then update the Metasploit running instance to the current version. Architecture of MetasploitThe architecture of Metasploit consists of various important components. These components are required to completely use Metasploit power: 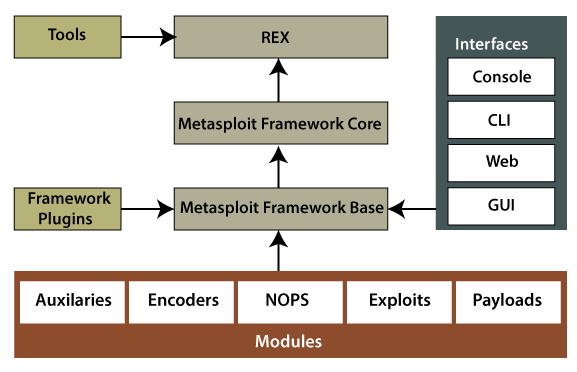
Advantages of MetasploitLet's discuss some advantages of Metasploit. 1. Open-sourceIt is actively developed and open-source is the most important reason why we prefer Metasploit. Several other paid tools exist to carry out the penetration testing process. However, Metasploit permits users for adding their custom modules and accessing its code. The Metasploit Pro version is chargeable, although, for the sake of gaining, the community edition is preferred mostly. 2. Easy naming convention and support to test large networksMetasploit is easy-to-use. However, here this feature defines the easy naming conventions of many commands. Metasploit facilitates ease while building a large penetration test of a network. For example, suppose we have to test any network having 200 systems. Rather than testing all the systems one-by-one, Metasploit can test the whole range automatically. With parameters like Classless Inter-Domain Routine (short for CIDR) and subnet values, Metasploit can test every system to exploit the susceptibility. However, in any manual exploitation method, we may need to define the exploits onto 200 systems manually. Therefore, Metasploit is saving a large amount of energy and time. 3. GUI EnvironmentMetasploit provides third-party instances and friendly GUI like Armitage. These types of interfaces can ease the projects of penetration testing by facilitating services like functions on a button click, vulnerability management over the fly, and easy-to-shift workspaces. 4. Cleaner exitsMetasploit is liable to make a cleaner exit through a system. It is an important aspect if we know that this service will not immediately reboot. Also, it gives a lot of functions for post-exploitation like persistence which could support to maintain access to a server permanently.
Next TopicParaphrasing Tools
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










