Difference between Security and Privacy
What is Security?
Security can be defined as the freedom from potential harm caused by others. Security may be caused by social groups and persons, institutions and objects, ecosystems and other phenomenon or entities susceptible to some unwanted changes.
Mostly, security is defined as protection from various hostile forces. However, it contains a variety of other aspects. For example, harm absence, resilience against harm or damage, secrecy, containment, etc.
The term is also used to define systems and acts whose objective is to provide security. For example, remote guarding, security cameras, cybersecurity systems, security guard, security forces, and security companies.
Security contexts (examples)
The following tables represent a few primary domains where various concerns of security are prominent:
IT
- Endpoint Security
- Network Security
- Digital Security
- Data Security
- Application Security
- Internet Security
- Computer Security
- Communications Security
Physical
- Security seal
- Border Security
- Security print
- Security bag
- Supply chain/Port Security
- Physical Security
- Infrastructure Security
- Home Security
- Environmental Security
- Food Security
- Corporate Security
- Airport Security
Political
- Human Security
- International Security
- Internal Security
- Homeland Security
- Public Security
- National Security
Monetary
- Social Security
- Financial Security/Economic Security
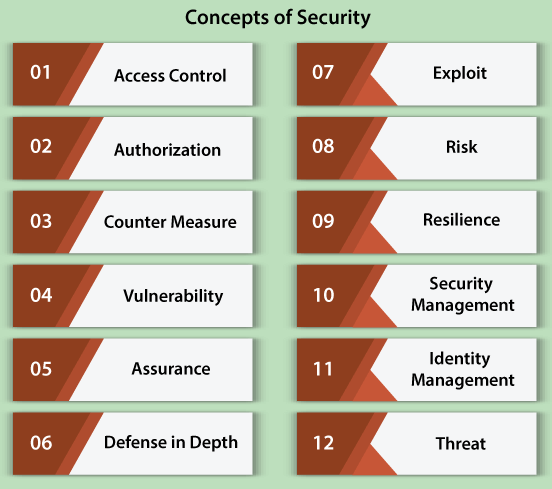
Concepts of Security
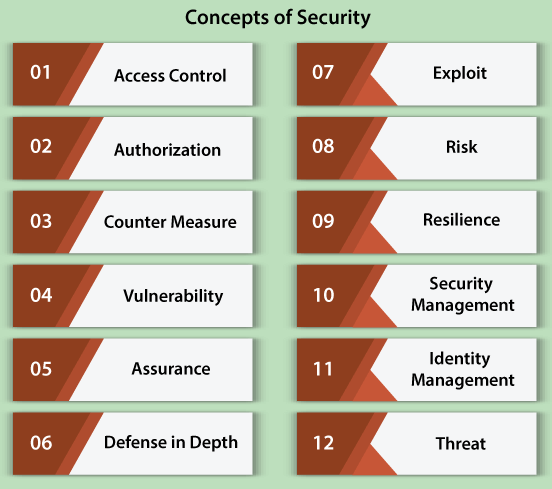
Certain concepts persist throughout distinct security fields:
- Access control: Some selective access restrictions to any place or various other resources.
- Authorization: The action of specifying privileges and rights of access to resources regarding computer security and information security in general.
- Counter measure: A way of preventing a system or act from having several intended consequences.
- Vulnerability: A degree to which something can be modified (in an unwanted way usually) by independent forces.
- Assurance: A confidence expression that a measure of security will implement as expected.
- Defense in Depth: A variety of thoughts, such that several security measures can enhance security.
- Exploit: A way of capitalizing over vulnerability inside a security system (cyber-security system usually).
- Risk: A feasible event that can cause loss, harm, damage, etc.
- Resilience: A degree to which a system, nation, community, or person can resist adverse independent forces.
- Security management: Recognition of the assets of an organization (including information, system, machines, buildings, people assets), which are followed by the implementation, documentation, and development of procedures and policies to protect these assets efficiently.
- Identity management: Allows the right users to access the right holdings at the right time and for the right sense.
- Threat: A source of damage.
Security Advantages
Let's discuss the advantages, which are listed below:
- Guaranteeing or deletion of malicious components in the preexisting network.
- Protection from mischievous attacks on our network.
- Restrict people from unauthorized entry to any network.
- Protecting confidential information.
- Restricts programs from some of the resources that might be infected.
Security Disadvantages
The disadvantages are listed below:
- Complicated to work with various non-technical users.
- Strict regulations.
- Restrictive for several resources.
- Being attacked constantly.
- Needs patching constantly.
What is Privacy?
Privacy can be defined as an individual or a group's ability to cloister the data about them and then reveal it selectively.
It means that privacy is applied to sensitive or crucial information. The privacy domain overlaps moderately with security that can add the concepts of proper use and protection of data.
The concept of global specific privacy is a modern concept mainly associated with Western culture (North American and British in particular) and remained unknown virtually within a few cultures. Most cultures identify the ability of persons to withhold some parts of personal information through wider society.
In the organizational world, an individual can volunteer secret details to receive a few sorts of profit. Public figures can be subject to regulations and rules on its interest. Secret information of a person that is shared voluntarily and misused can subsequently cause identity theft.
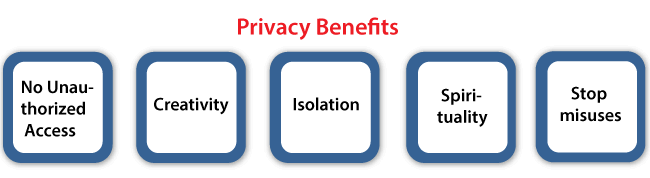
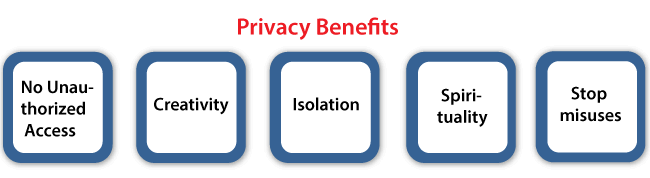
Privacy Benefits
The benefits are listed below:
- Unauthorized users cannot access our personal data.
- All aspects of our life are not transparent.
- Creativity
- Privacy can be defined as the "moral capital."
- Isolation
- Spirituality
- Different relationships with distinct people.
- It makes users feel protected about their data and information.
- No misuse or unwanted attacks.
- Encourages customers for sharing and shopping information with organizations.
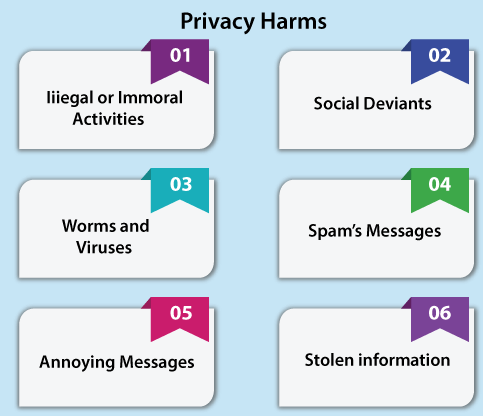
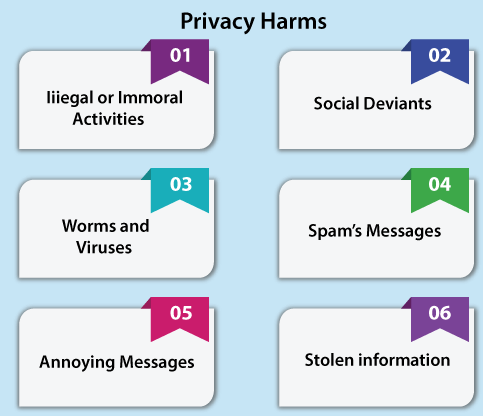
Privacy harms
Let's discuss the threats to our privacy:
- Can cause illegal or immoral activities
- Social deviants
- Worms and viruses
- Spam's messages
- Annoying messages
- Stolen various card information
- Family violence
- May lead to unhappiness
- Trapped/caught in relationships
Difference between Security and Privacy
| S. No. |
Security |
Privacy |
| 1. |
Security is something about data safeguarding. |
Privacy is something about user identity's safeguarding. |
| 2. |
Security can be defined as protection against various unauthorized access to information. |
Privacy can be harder to specify because user-specific information can be secure information as well. |
| 3. |
Example: Clinic staff and hospital apply secure systems for communicating with patients regarding their health-related information, rather than transferring information by email accounts. |
Example: It might limit the record access of patient health to particular staff members of the hospital, like medical assistants, nurses, and doctors. |
| 4. |
Security is any state of being free through potential threats or personal freedom. |
Privacy indicates anyone who feels free from any unwanted attention. |
| 5. |
There are three primary objectives of security such as availability, integrity, and confidentiality. |
On the other side, privacy represents many rights of organizations and individuals related to personal data. |
| 6. |
The security programs represent the set of regulations and protocols to protect each confidential information resources and assets that an enterprise owns and collects. |
Privacy programs concentrate on safeguard personal information only like passwords, log-in credentials, etc. |
| 7. |
The three primary security principles are promoting the availability of information and data, preserving the integrity of data assets, and protecting confidentiality. |
To a few extent, privacy is achieved with the initiatives of security and security relies on the phpMyAdmin privacy of access and credentials of data. |
| 8. |
Security can be accomplished without privacy. |
Privacy can't be accomplished without security. |
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now










