AES 256 Encryption in JavaSecurity has become an important aspect nowadays. Java programming provides security for data transfer as well as communication between several nodes by supporting different encryption and hashing algorithms. In this section, we will discuss the AES 256 encryption algorithm and implement the logic in a Java program. What is AES?AES is an Advanced Encryption Standard algorithm. It is a type of symmetric, block cipher encryption and decryption algorithm. It works with key size 128, 192, and 256 bits. It uses a valid and similar secret key for both encryption and decryption. In AES, the block cipher is used. It means that the data to be encrypted is converted into blocks for encryption. The original data value is encrypted using different bits of padding such as 128, 192, or 256 bits. Advantages of AES
Disadvantages of AES
AES 256 Encryption and Decryption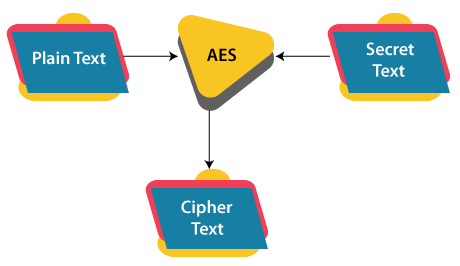
Modes of Operation of AES AlgorithmThere are the following six modes of operation in the AES algorithm: 1. ECB (Electronic Code Book): It is the simplest mode among all. It divides the plaintext message into blocks of size 128 bits. Then these blocks are encrypted using the same key and algorithm. Hence, it generates the same cipher text for the same block every time. It is considered a weakness and therefore it is suggested not to use ECB for encryption. 2. CBC (Cipher Block Chaining): CBC uses an Initialization Vector (IV) to improve the encryption. In CBC, the encryption is performed by XOR operation between the plaintext and IV. Then the cipher text is generated. It then uses the encryption result to XOR with the plain text until the last block. 3. CFB (Cipher FeedBack): CFB can be used as a stream cipher. It encrypts the initialization vector (IV) first and then XOR with the plaintext to generate the cipher text. Then it encrypts the cipher text with the next plaintext block. In this mode, decryption can be performed in a parallel manner but encryption cannot be performed in a parallel manner. 4. OFB (Output FeedBack): OFB can also be used as a stream cipher. It does not need padding data. First, the IV is encrypted and then the encryption result is XOR with the plaintext to generate the cipher text. Here, the IV cannot be encrypted or decrypted in a parallel manner. 5. CTR (Counter): In CTR mode the encryption process is similar to OFB mode, the only difference is that it encrypts the counter value instead of IV. It has two advantages, encryption or decryption can be performed in a parallel manner and the noise of one block does not affect another block. 6. GCM (Galois/Counter Mode): GCM mode is an extended version of CTR mode. It was introduced by NIST. The GCM mode provides the cipher text as well as authentication tag after the encryption process. In the following program, the AES/CBC/PKCS5Padding algorithm is used as it is popular and used in many projects. AES-256 Encryption and Decryption Java ProgramAESExample.java Output: Original value: AES Encryption Encrypted value: V5E9I52IxhMaW4+hJhl56g== Decrypted value: AES Encryption In the above Java program, the AESExample class defines two methods, encrypt() that implements the AES-256 encryption algorithm and decrypt() that implements the AES-256 decryption algorithm. And lastly, the driver method gives a call to both the methods and displays the result on the console. In this article, we have discussed the AES 256 encryption algorithm in Java, its modes of operations with its implementation as well as its pros and cons.
Next TopicApplications of Array in Java
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









