Firestore setup and configurationIn our previous section, we learned about the Cloud Firestore, its key capabilities, features, and how it works. Now, we will discuss how we set up and configure an Android application with Firebase to use Cloud Firestore in our application. Just like Firebase Real-time Database and Firebase Authentication, Firestore's starting steps are the same and will use Kotlin. So, let's start with the starting steps and elaborate each step, which is performed to set up and configure the application to use Firestore in Firebase. Step 1: In the first step, we will create a new Android Studio project with an empty activity and Kotlin language and give it name FirestoreExample. 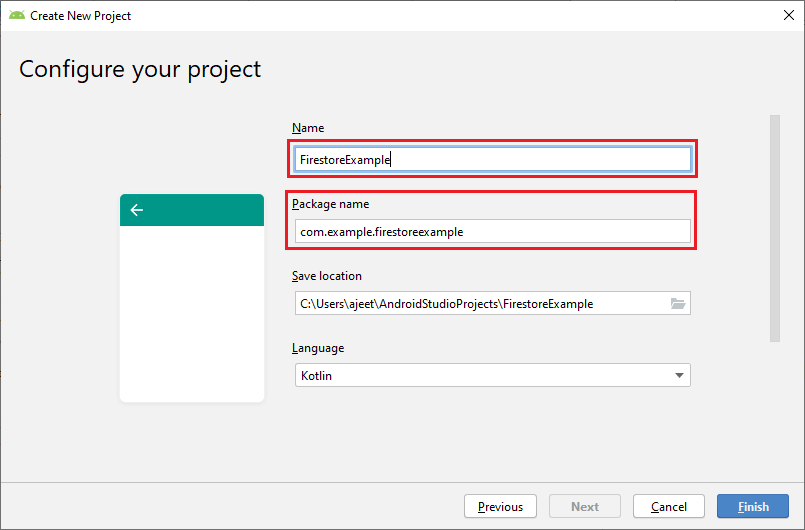
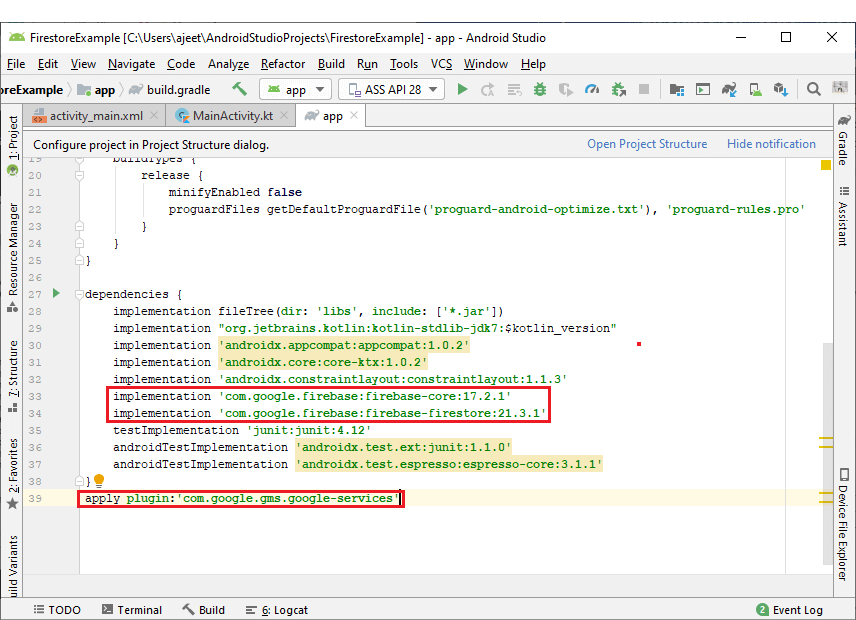
Step 2: In the next step, we will connect our Android Application with the Firebase either from Firebase Assistant or manually using console. After that, we will add all the required libraries and plugin to our app.gradle file. And we will also add mavenLocal() as our repository and all projects. 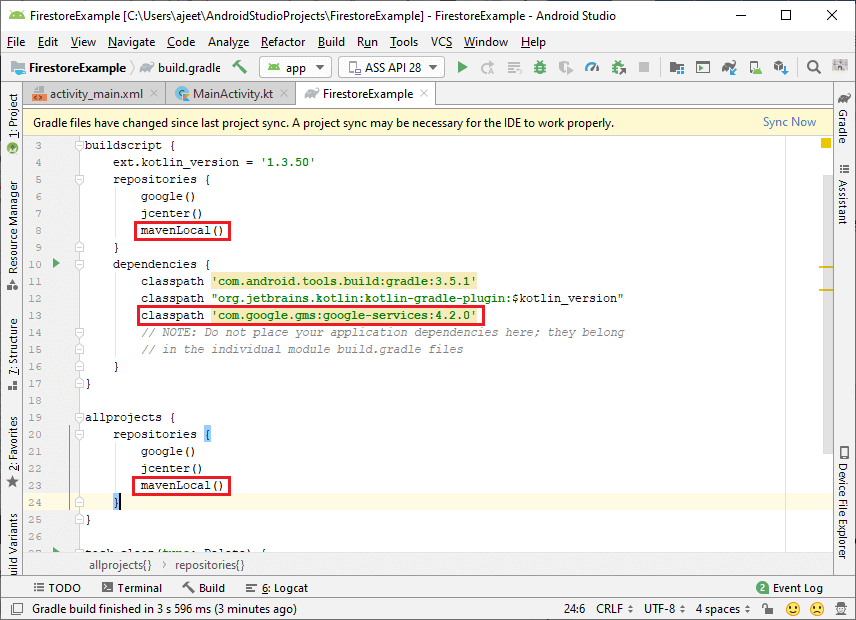
Step 3: Go to the Firebase console and look at the Real-time database. In Developers-> Database, there will be two options, i.e., cloud Firestore and Real-time database. 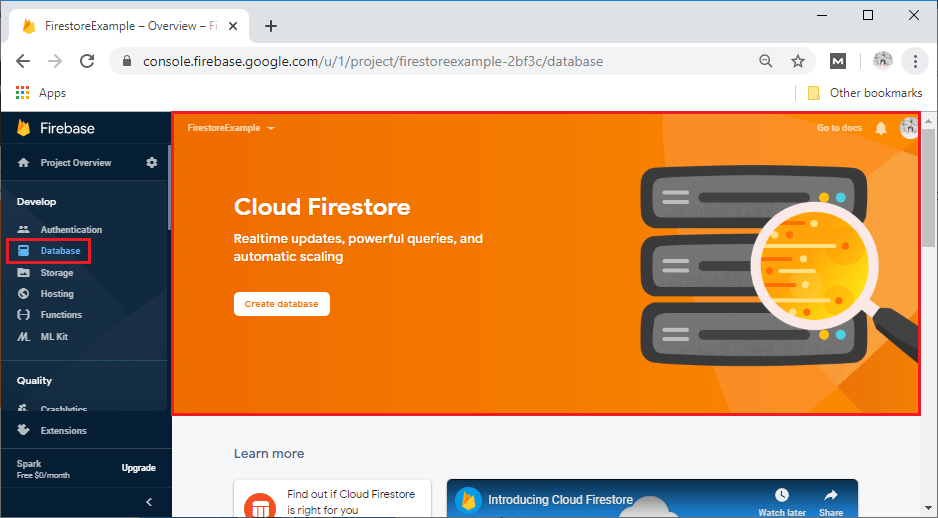
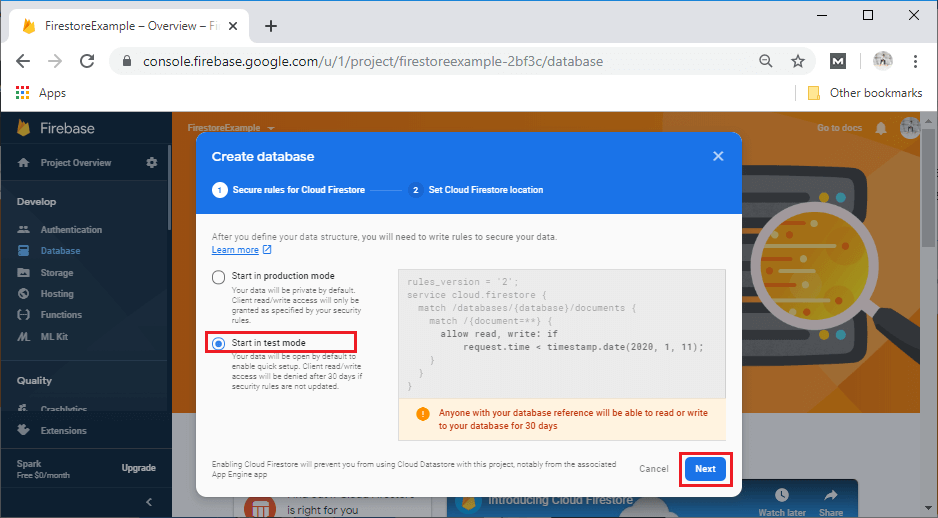
Step 4: In the next step, we will create a database by clicking on the Create database. After clicking on Create database, a popup box is open where we create a database with specific rules. We will use it as a test mode, so select to start in test mode. And last click on next. 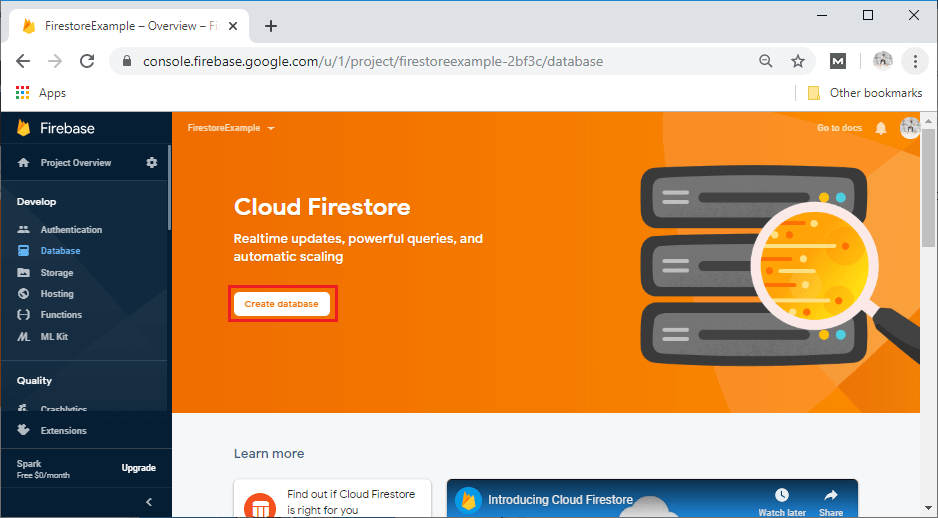
After clicking on Next, a popup box will open. Here, we can select our Cloud Firestore location depending on where we want to locate. At last, click on Done. 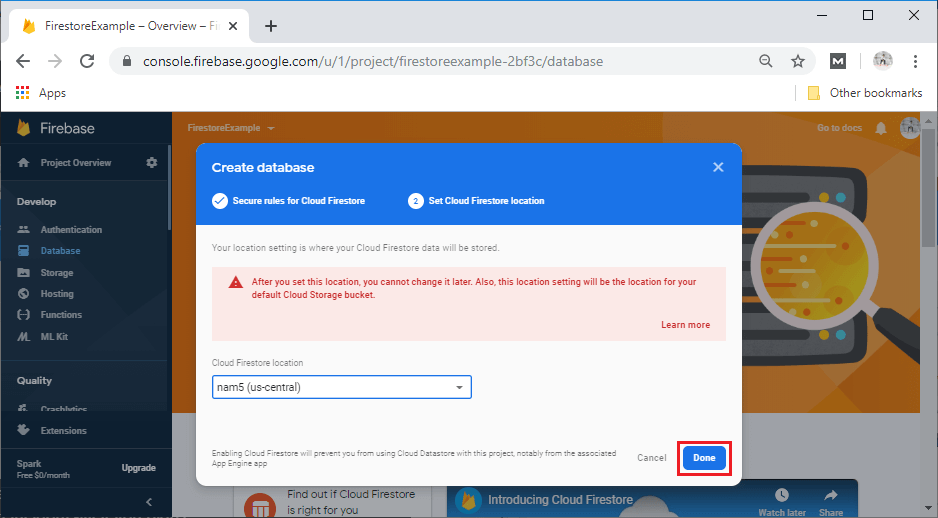
Step 5: After clicking on Done, a Firestore Database will be created, which will look a little bit different from the Real-time Database. Here, we have Data, Rules, Indexes, and, Usage for data storing, security rules, indexes, and usage, respectively. 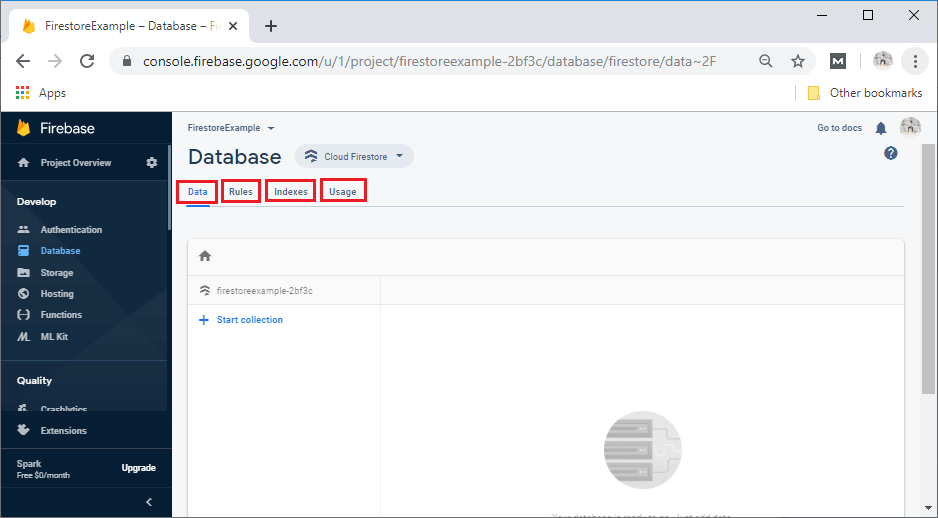
Step 6: Now, change our security rules because, by default, anybody can access our database right now. The changes will be done in such a way that only authenticated users can access the database. And after making changes, we will publish them. The security rules are defined as: 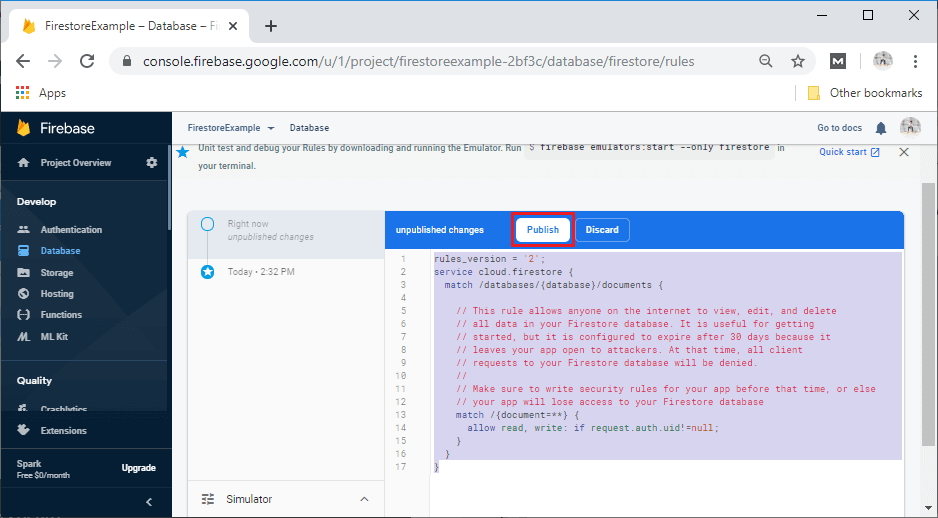
Setup and configuration are completed here, and now we can implement our code manipulation of data.
Next TopicData Organization in Firestore
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









