Brute Force Meaning
A Brute Force attack can be defined as an error or trial technique used by various application programs for decoding encrypted data like DES (Data Encryption Standard) or password keys. An application of Brute Force attack proceeds from each possible set of legal characters within the sequence.
The hackers can apply the Brute Force attacks to obtain access to any account or website, shut a site down, steals data, or executes other attack types. Brute Force attacks can be considered as a time consuming although infallible approach.
Sometimes, the crackers are used inside an enterprise for testing network security.
Some key points of brute force attacks are as follows:
- The brute force attacks apply trial-error for guessing encryption keys, login info, or detect an unknown web page.
- Brute Force means that they apply extra forceful attempts to try and force the way into our private accounts.
- It is an old method of attack but still popular and effective with hackers. Depending on the password's complexity and length, cracking may take anywhere through many years or may a few seconds.
Brute Force Attack Working
The Brute Force attack will apply automated tools for guessing several username and password combinations until they detect the accurate input.
Distinct brute Force attack types exist. A most common form of Brute Force attack is credential recycling where passwords and usernames are used through previous attacks. The reverse brute force attack starts by attacking including the password as any known value but not the username. Then, the hacker will follow a similar pattern as a general brute force attack for detecting the accurate username.
Another type of Brute Force attack is a dictionary attack where each word within the dictionary will be tested for finding the password. Also, dictionary attacks can augment words along with characters, numbers, and more. Some other additional types of Brute Force attack may use and try the most used passwords like "12345678," "password," etc.
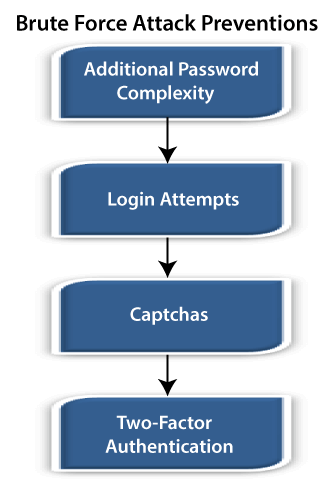
Brute Force Attack Prevention
There are some common forms to prevent brute force attacks, which are discussed as follows:
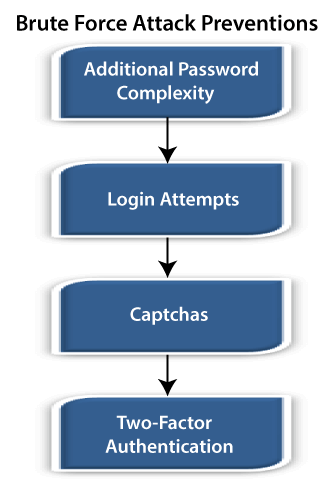
- Additional Password Complexity: This technique will make the procedure of guessing any password take longer significantly. A few websites will need an 8-16 characters password along with at least a number or letter with special characters (like "."). Some websites will not allow any user to include their ID, username, or name in the passwords.
- Login Attempts: Additional login attempts will block out the users for any specified time amount that exceeds any specified attempts amount in inputting usernames/passwords.
- Captchas: There are some boxes in these captchas. These boxes will display warped text and confirms to the user what the text within the box is. It will prevent bots from running various automated scripts that will appear within the brute force attacks, although being easy for humans to pass by.
- Two-Factor Authentication: It will add a security layer to the main authentication form. Two-Factor authentication needs two authentication forms. For example, for singing into a new Apple device, the users will have to put within the Apple ID with the six-digit code, i.e., shown on other devices marked as trusted previously.
A better way to secure against the brute force attack is to apply each or a set of the strategies mentioned above.
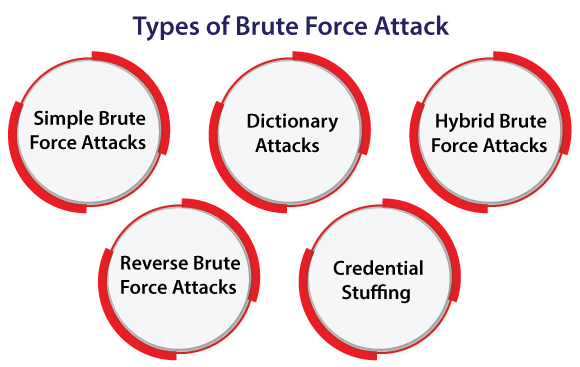
Types of Brute Force Attack
All brute force attacks could use distinct types of techniques for uncovering our sensitive information. The types of brute force attacks are discussed as follows:
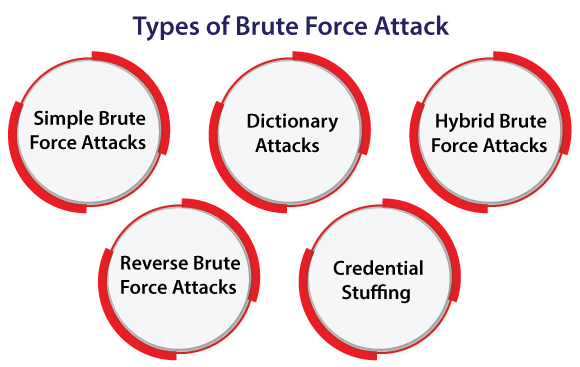
- Simple Brute Force Attacks: Various hackers attempt for guessing our credentials logically- completely unassisted through many types of software tools. These could reveal simple PINs and passwords. For example, passwords like "guest12345".
- Dictionary Attacks: The hacker selects a target and executes feasible passwords against the username within the standard attack. These are called dictionary attacks. These attacks are the most common attacks in brute force attacks. Often, these are used as the necessary element for password cracking. A few hackers execute from augment words, unabridged dictionaries, etc.
- Hybrid Brute Force Attacks: Hybrid attacks can be defined as a combination of brute force attacks and dictionary attacks. These attacks can be used for detecting combo passwords which mix various common words along with some random characters. An example of brute force attacks of this type of nature will include passwords like Spike1234 or NewYork1993.
- Reverse Brute Force Attacks: As its name implies, these attacks can reverse the strategy of attacks by beginning with any known password. After that, hackers will find a lot of usernames as far as they detect a match. A lot of criminals begin with some cracked password that is available online through existing breaches of data.
- Credential Stuffing: When the hackers have a combo of username-password working for only a single website, they will try this combo on other websites also. Since the user has been acknowledged for reusing the login data across various websites, they're the targets of any attack like credential stuffing attacks.
Here is how hackers profit from brute force attacks:
Collecting activity data or profiting through ads: Hackers can harm websites alongside others for earning advertising commissions. Some of the popular ways of doing this are as follows:
- Inserting spam ads over an experienced site for making money all time. The ad is viewed and clicked by so many visitors.
- Rerouting the traffic of a website to ad sites.
- Spyware is commonly affects the sites or visitors by tracking malware or activity. Information is taken by advertisers without our content for helping them develop their business.
Stealing personal valuables and data: Cracking open the bank vaults could be like breaking into many online accounts (everything from all bank accounts to each information of tax could be detected online). Criminals may steal our money, identity, or sell our private data for benefit. Sensitive databases through an enterprise can be uncovered within the corporate-level breaches of data.
Spreading malware for causing disruptions: when a hacker wishes for causing practice or trouble their skills. The hackers can redirect the traffic of a website to mischievous sites. They might directly affect a website with buried malware to be installed over the systems of visitors.
Hijacking our system for mischievous activity:
Hackers enlist a lot of unsuspecting devices known as a botnet for speeding up the efforts if a single machine is not enough. Malware may infiltrate our mobile devices, computer, or online accounts for increased brute force attacks, spam, phishing, and many others. We may be high at risk of affection if we don't have any antivirus system.
Ruining the reputation of the website:
The cybercriminals may decide for infesting our website with improper content if we run any website and become the target of vandalism. It may include audio, images, the text of a racially, pornographic, or violent offensive behavior.
Helping tools for Brute Force attempts
Various Hackers have improved tools for doing the job much faster because guessing the passwords for a specific site or user can take more time.
Automated tools aid with brute force attacks: Automated tools use guessing that is created for building each possible attempt and password to apply them. Hacking software of brute force can detect one dictionary word password in a single second.
These types of tools include workarounds programmed within them for:
- Permit hackers for cracking wireless modems.
- Work against various protocols of computer (like Telnet, SMTP, MySQL, and FTP)
- Recognize weak passwords
- Covert words into leetspeak, for example, "don'thackme" becomes "d0n7H4ckm3".
- Decrypt passwords into encrypted storage.
- Run dictionary attacks
- Operate each possible character combinations.
A few tools scan rainbow tables (pre-compute) for outputs and inputs of well-known hash functions. The hash functions can be defined as the encryption methods that are algorithm-based. These methods are used for translating passwords into fixed and long-length series of numerals and letters. Rainbow tables erase the brute force attacking hardest part for speeding up the process.
GPU speeds attempts of brute force
The brainpower of so many computers is required for running software of brute force password. Hackers have implemented the hardware solutions for making this job part much easier, unfortunately.
Combining GPU and CPU:
GPU (Graphical Processing Unit) speeds up the power of the computer. By adding a lot of cores of computer in GPU for processing. It enables the computer for managing more the one task at the same time. GPU processing can be used for engineering, analytics, and other types of computing-intensive programs. Hackers applying this technique can crack the passwords 250 times faster as compared to the CPU alone process.
Steps for protecting password for professionals
We can take the precautions and also support others to keep our network safe. Network security and user behavior systems will require reinforcement.
For users and IT professionals, we can take normal pieces of suggestions:
- Erase unused accounts along with the high-level permissions: Unmaintained account is a vulnerability we can't risk. Keep it away as early as possible.
- Use leading passwords and usernames: Leading passwords can help out to protect us from various attacks. These are stronger than password1234 and admin for keeping out the attackers.
Passive backend security for passwords
- Salt the hash: Also, administrators should normalize password hashes by including numbers and letters random string (known as salt) to any password itself. The string must be saved in an isolated database. These strings can be added and retrieved to a password before it is hashed. Users with a similar password contain different hashes by salting a hash.
- High encryption rates: System administrators must ensure that the password for the systems is encrypted with the highest encryption rate like 256-bit encryption. It should be done for making it more complex for attackers to succeed.
- Limit login retries: By limiting the attempts, we can decrease the vulnerability to brute force attacks as well. For example, permitting three attempts for entering the accurate password before blocking out any user for a long time can cause important delays. Also, it can cause hackers for moving on to other easier targets.
| 
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now










