Phishing Attack MeaningPhishing is electronic communication's fraudulent used to take and deceive the user's advantage. Phishing attacks try to grab confidential and sensitive information like network credentials, credit card details, passwords, usernames, and much more. By representing as an appropriate institution and individual via email or phone, cyber attackers apply social engineering for manipulating victims into executing particular attacks- such as click on any malicious attachment or link, or admitting confidential information. Organizations and individuals both are at high risk; almost every organizational and personal data is valuable. In addition, a few scams of phishing can target enterprise data for supporting state-backed spying or espionage efforts on the opposition groups. "Phish" is just like it is spelled. It is pronounced as the "fish" word. This term was introduced in the middle of 1990s between hackers objecting for tricking AOL users into providing the login data. The "ph" can be described as any part of the tradition of whimsical hacker spelling. Probably, it was affected by the "phreaking" term. It means "phone phreaking". It was an early way of hacking which involved playing music tones into mobile handsets for getting phone calls free of cost. Methods of PhishingMost often, phishing attempts to start with the email attempting for obtaining various kinds of sensitive information from a few user interactions, like download any affected attachment or click on any malicious link.
Note: Also, the scams of phishing can employ social media tools, text messages, and phone calls for tricking victims into giving sensitive information.Examples of Phishing AttacksThe following examples represent the common attempts of phishing scams:
Phishing Attacks TypesA few phishing scams specific types that uses targeted methods for attacking certain organizations and individuals. The different types of phishing attacks are: 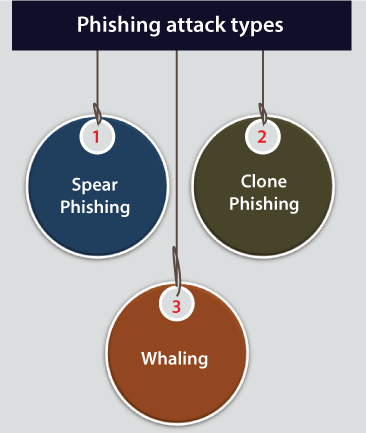
Spear PhishingThe email messages of spear-phishing would not look as irregular as the normal phishing attempts. Often, attackers will gather data about the targets for filling emails with authentic context. A few attackers create highly personalized messages and hijack organizational email communications. Clone PhishingVarious attackers are capable to view appropriate and previously distributed email messages. They can create an identical clone of it, or copy. After that, te link is modified for something mischievous. WhalingSpecifically, whaling attack targets senior or high profile executives in the enterprises. Often, the whaling attempt's content will appear like any high-level managerial business or other legal communications. Phishing Attack PreventionPhishing attacks security needs steps to be grabbed by both enterprises and users. Vigilance is the key for users. Often, the spoofed messages include subtle errors that disclose the true identity. It can also include spelling changes or errors to the names of the domain. Also, users must stop thinking about how they are getting information like email. The step's number could be taken for mitigating both spear and phishing attacks for enterprises:
Next TopicBrute Force Meaning
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










