TensorFlow Security ? 5 main Loopholes in TensorFlowSecurity of TensorFlow includes significant issues such as TensorFlow models as programs, how to run untrusted models, and accepting the untrusted input. 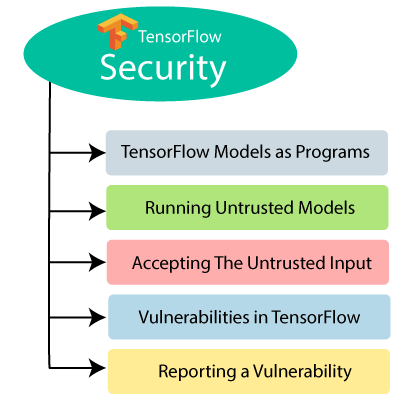
TensorFlow Models as ProgramsTensorFlow has its runtime system, which interprets and executes its programs. The program in TensorFlow is encoded as the computation graphs and stores the parameters separately as checkpoints. During the runtime, TensorFlow executes the computation graph with the parameters given. The behavior of the chart may change depending upon the change in settings. All of the tasks performed are done with the permission of the TensorFlow process. The TensorFlow models are like the programs and therefore need to be taken as such from the TensorFlow security perspective. Untrusted ModelsIt is a general that an untrusted model should first execute in a sandbox. There are many possibilities for any model to become untrusted, for instance, if some untrusted party provides TensorFlow kernel or provides python code required for TensorFlow graphs. TensorFlow Security is determined by the computational graph, whether the user-provided checkpoint is safe or not. Generally, creating a computational graph with malicious inspections can trigger uncommon and insecure behavior. Accepting the mistrustful inputAnyone can design models that are secure by providing the models to process the untrusted data safely. We suppose that we have not any bugs. An excellent way to analyze how the TensorFlow graph works, an interpreted programming language like Python. One can write a safe Python code that can easily expose to the user given inputs, but it is easy to write un-secure Python programs. Vulnerabilities in TensorFlowTensorFlow is an extensive complex system that depends on several third-party libraries for its use. TensorFlow model performs arbitrary computations that can read or write files or can communicate over a network. If the model shows other than these specifications, then that behavior can cause vulnerability. Reporting a VulnerabilityWe will see how to see the vulnerabilities in TensorFlow. We can send the reports about any issues regarding security to [email protected]. The report to the email is delivered to the security team in TensorFlow. The emails accept within 24 hours and provide a detailed response within a week, along with the next steps.
Next TopicTensorFlow Single and Multiple GPU
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share










