NetcraftIn this section, we will learn how to get information about the technologies which is used by the target websites. To do this, we are going to use a website called as Netcraft (https://www.netcraft.com), and then we will put the target address, and select our target as isecur1ty.org, and click on the arrow as shown in the following screenshot: 
After this, click on Site Report as shown in the following screenshot: 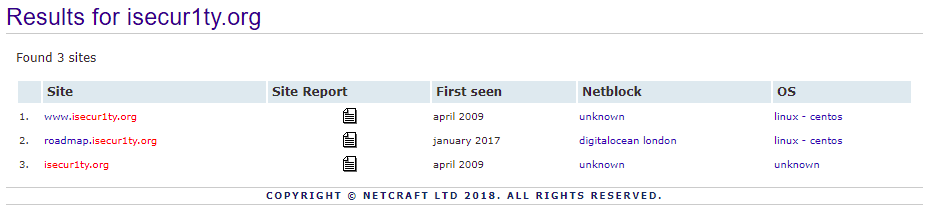
In the given screenshot, we can see some basic information like Site title, Site rank, Description, Keywords, and when the website was created: 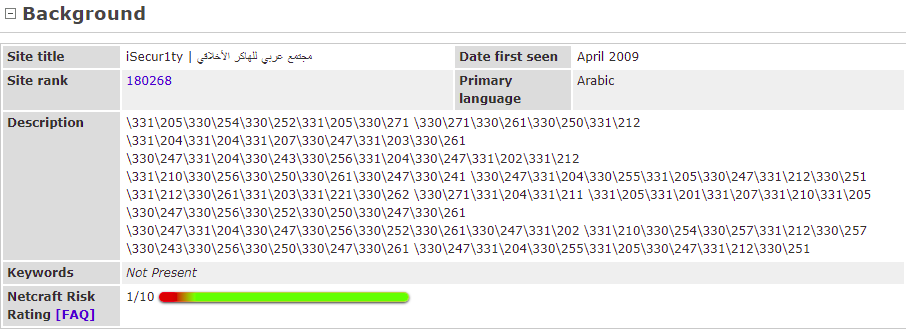
When we further scrolling down, we can see the website itself, the Domain, the IP address, and Domain registrar, which is the company who registered the domain for isecur1ty: 
In the preceding screenshot, we would normally see information about the organization, but here, we can't because isecur1ty is using privacy protection. Usually, we should be able to see such information and even more. In the preceding screenshot, we can see that it is hosted in UK, we can also see the Nameserver, which is ns1.digitalocean.com, and again, if we just go to ns1.digitalocean.com, we will discover that this is a website for web hosting. Now, we know that this is a web hosting company, and in worst-case scenarios, we can use this or try to hack into ns1.digitalocean.com itself to gain access to isecur1ty. If we further scroll down, we will see the Hosting History of the hosting companies that isecur1ty used. We can see that the latest one is running on Linux with Apache, the same server that we saw in the previous section, 2.2.31 with Unix mod_ssl and all the other add-ons: 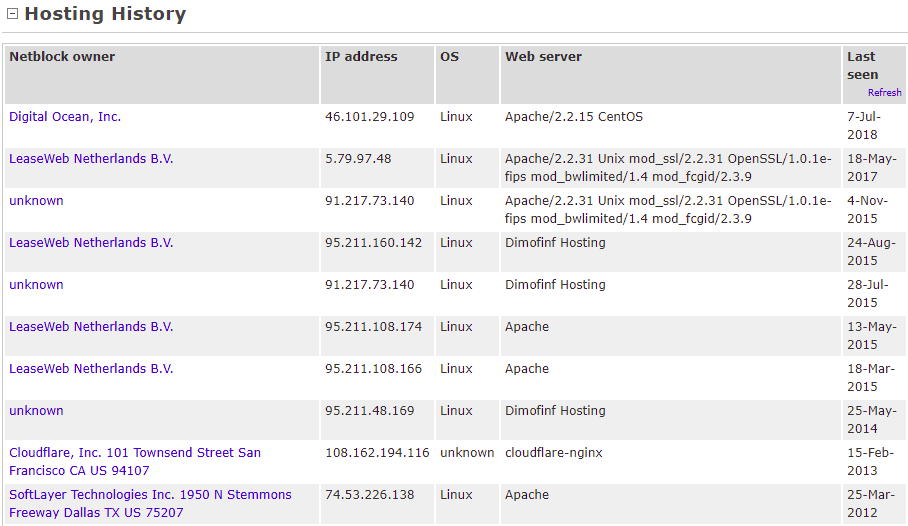
Again, this is very important to find exploits and vulnerabilities on our target computer. Scrolling down to Web Track ers, it will show us the third-party applications used on our target, so we can see that our target uses MaxCDN, Google, and other Google services. This could also help us to find and gain access to the target computer as shown in the following screenshot: 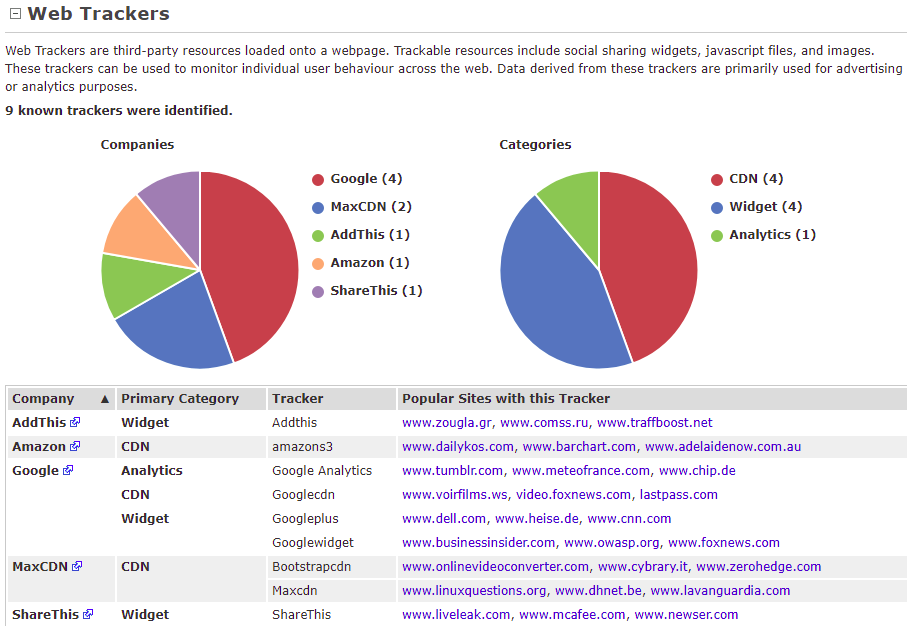
The Technology tab shows us the technologies which are used on the target websites: 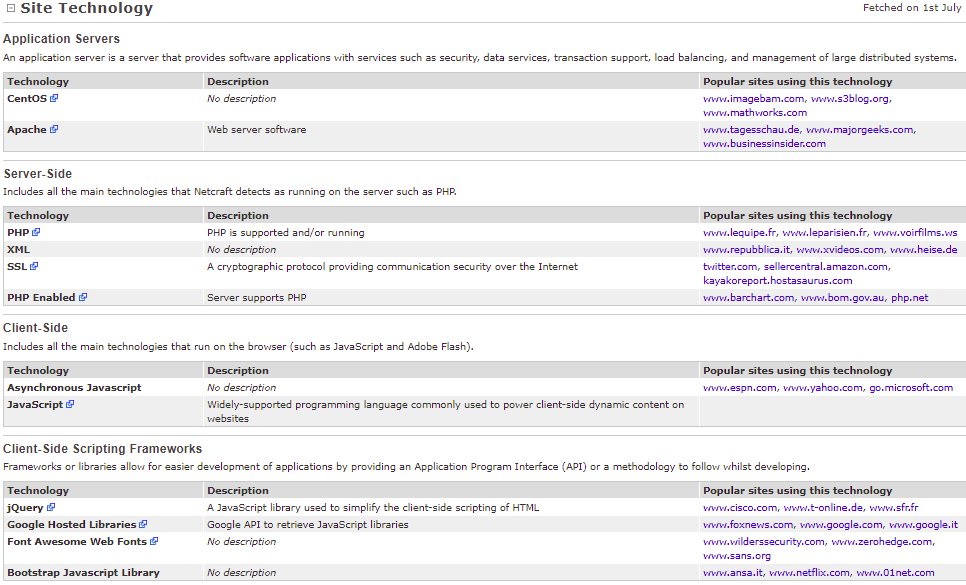
In the above screenshot, we can see that it is using the Apache web server. On the Server-Side, we can see that the website uses PHP, which means the website can understand and run PHP code. In future, if we manage to run any kind of code on our target, then the code should be sent as PHP code. To create payloads on Metasploit or on Veil-Evasion, we should create them in PHP format and the target website will be able to run them because it supports PHP. On the Client-Side, we can see in the preceding screenshot that the website supports JavaScript, so if we run JavaScript on the website, it would not be executed on the website, it will be executed on the users side who are viewing the websites, because JavaScript is a client-side language and PHP is server-side. If we manage to run PHP code, it will be executed on the server itself. If we manage to run JavaScript, it will be executed on the users. It is same as jQuery. This is just a framework for JavaScript. In the following screenshot, if we are scrolling down, then the website uses WordPress Self-Hosted software. Netcraft will show any web applications being used on the website: 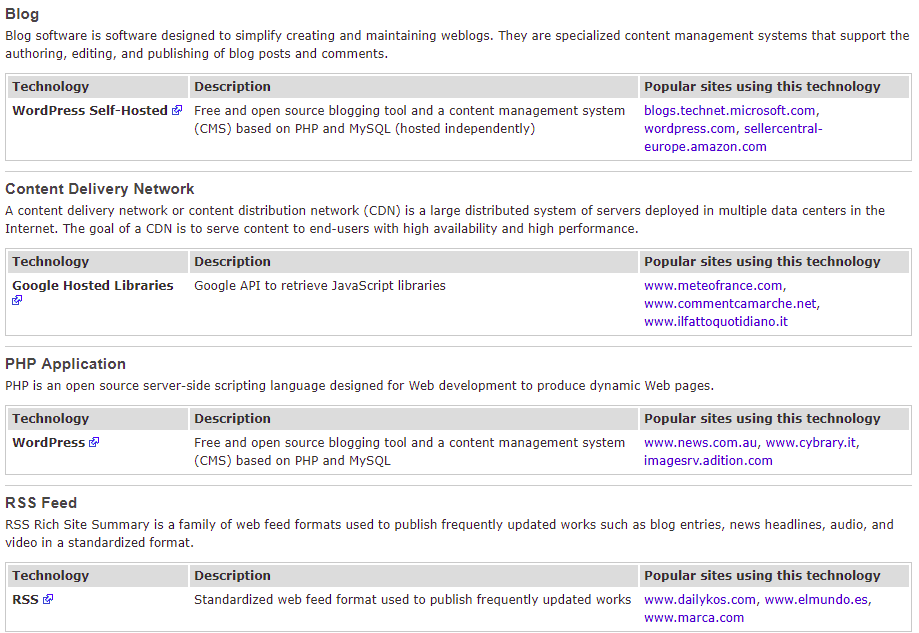
WordPress is just a web application, so we could see other example in our case, and it is an open source web application, there are a lot of other websites might have. If we are lucky enough to find an existing one, then we can go ahead and exploit it on the target website. For example, suppose we have WordPress and if we go to https://www.exploit-db.com/ and search for WordPress, we will able to find a lot of exploits related to WordPress. There are different versions of WordPress. We need to make sure that we have the same number of version as our target. We will look at an example to see how to use exploits, but it just shows how powerful information gathering is. If we further scroll, we will find other information like the websites uses HTML5 and CSS, and all kind of stuff as shown in the following screenshot: 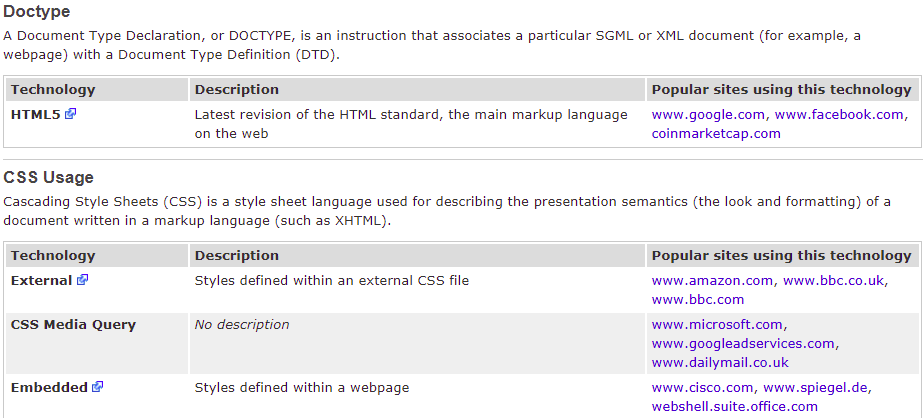
Hence, Netcraft is used for getting to know the website. We gathered information regarding the site that it runs on PHP, and runs JavaScript. It uses WordPress, so we can use WordPress to hack into the website. If we scroll up, we also discovered web hosting of the website. So, in the worst-case scenarios, we can try to hack into a web hosting server and gain access to our target website.
Next TopicRobtex
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









