Installing VeilIn this section, we are going to learn how to generate a backdoor that is not detectable by antivirus. A backdoor is just a file, and when that file is executed on a target computer, it will give us full access to that target machine. There are a number of ways of generating backdoors, but we are interested in generating a backdoor that is not detectable by antivirus programs. This actually is not hard to do, if we use a tool called Veil-Evasion. We are going to download the latest version of the Veil, which is 3, using the following GitHub link: https://github.com/Veil-Framework/Veil GitHub is a version control system that allows the programmers to post, share, and update source code. It is used a lot when downloading programs. Veil's repository can either be downloaded via GitHub's link or by copying it to our terminal. The following screenshot shows the GitHub's link that we have to copy: 
Now, before we download it, we actually want to store it in a /opt directory. So we are going to do cd to navigate to a different directory, and we are going to put /opt to open a directory called opt. Now we will run ls to list the available directories, we will see that we only have one directory for a program called Teeth. 
Now, if we want to download Veil, we have to copy the repository link from GitHub as shown in the above screenshot. Then we will go to our Terminal, to locate where we want to download it. So the first thing we are going to do is change the directory to /opt, and then we will put git clone, and input the URL of the repository. The command is as follows: 
Here, clone command is used to tell the git that we want to clone or download this framework, program, or project, before sharing the link with the Veil. To download the desired project, simply hit Enter, as shown in the following screenshot: 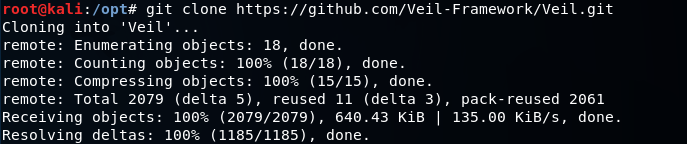
If we use the ls command to list our files, we should see a new directory called Veil. We are able to navigate to that directory by inputting cd Veil/. The ls command is used to list all the available files, including Veil.py, which we need to install. To do this, navigate to the config directory by inputting cd config/, and then run setup.sh bash script. This script will install Veil-Evasion. To run an executable from the terminal, we enter the ./ and then the name of the executable which is setup.sh, as shown in the following screenshot: 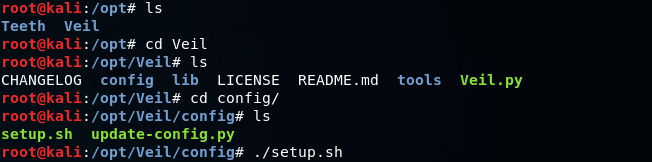
The above command should generate the following results: 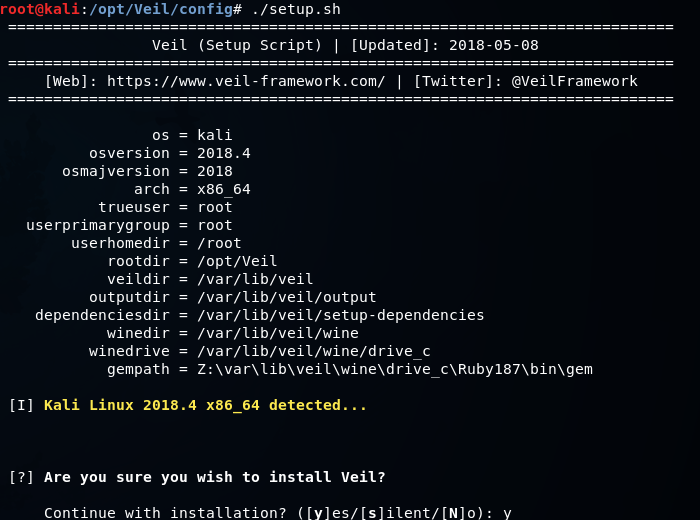
In the above screenshot, we can see that we are being asked if we want to install Veil, we should do y. Note that the installation may take a while. After installation, we first open our Terminal, and then we are going to navigate to the opt directory by inputting cd /opt, because that is where we cloned Veil. So, we are going to inputting the cd Veil/ command to change the working directory. Now we are inside the Veil directory. If we run ls command, we will see that we have Veil executable. So we can run this executable by putting ./ followed by the name of an exploit which is Veil.py. 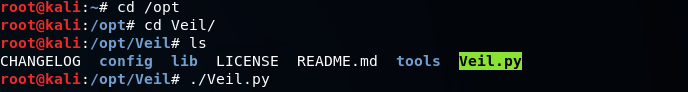
Now we are going to launch the above command, leading to the welcome screen for Veil, as shown in the following screenshot: 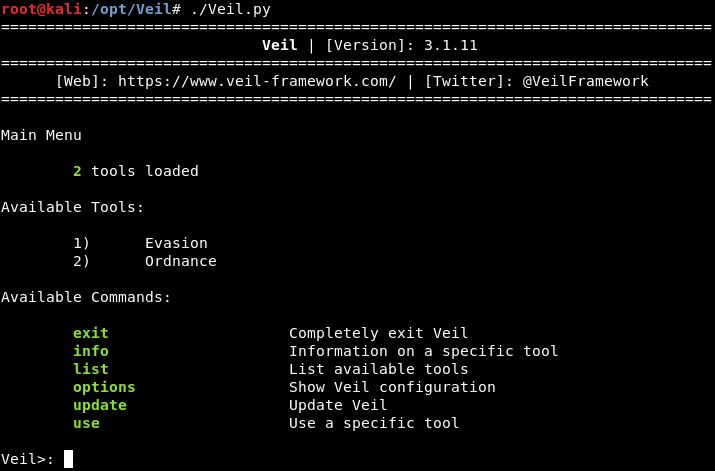
In the above screenshot, we can see that we Veil has two tools. In the next section, we are going to learn the usage of this tool.
Next TopicOverview of Payloads
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









