CRC program in CThere is a chance that noise during the data transmission process will alter the digital signals carrying the data from the sender to the receiver. Data supplied by the sender may not match data received by the recipient as a result. An error is what we term a change in a data bit, and to avoid one, the data received by the receiver is examined using various error detection techniques. The Cyclic Redundancy Check algorithm is one such example. Scope
IntroductionThe Cyclic Redundancy Check algorithm checks for errors and verifies the accuracy of the data delivered by the sender. CRC requires a generator polynomial in order to compute the check value using binary division in addition to the data that has to be transferred. To ensure that the data is genuine, the check value or CRC is sent with it to the recipient. The degree of the polynomial can be used as the bit locations to represent the data that will be conveyed to the recipient in polynomial form. The binary data 1010101 of length 7 can be, for instance, represented as, x7+x5+x3+1 As the value of that representation is also 0, the bit value of 0 is not represented. Binary data can also be used to represent the generating polynomial. The degree of the data polynomial must be less than the degree of the generator polynomial and must be larger than 0. Based on the degree of the generating polynomial, the CRC may be divided into several standards. Using a generator polynomial of degree 8 for the CRC-8 standard and degree 16 for the CRC-16 standard. This is a straightforward illustration of the generator polynomial. x5+x4+x2 It should be noted that Cyclic Redundancy Check may also be employed as a hashing function. Nevertheless, since CRC-8 can only yield 256(28). The following are the CRC's steps: the sender's side,
Check value, or CRC, is represented mathematically as, 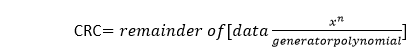
The n in this case refers to the generator polynomial's number of bits. Towards the receiver,
The stages in binary division are identical to those in regular polynomial division and are as follows:
One of the intriguing characteristics of the Cyclic Redundancy Check is the following procedure: CRC(x^y^z) == crc(x)^ crc(y)^ crc (z). The XOR function is represented by the symbol ^. If we XOR three pieces of data and then CRC the result, the CRC result will be the same as if we CRC each piece of data separately and then XOR with the results. NOTE: When both inputs are the same, the XOR operator returns 0, and while in all other circumstances it returns 1.CRC implementation in CThe CRC program may be put into use in C using one of two techniques. The first approach makes use of a character array, whereas the second approach makes use of bit manipulation strategies. Algorithm The CRC program's implementation algorithm is as follows:
The CRC function's algorithm is as follows:
The following truth table of the XOR operator serves as the foundation for the method employed in the XOR function:
The following is the algorithm used to check for faults on the receiver side:
CODE: OUTPUT: Enter data to be transmitted: 1001101 Enter the Generating polynomial: 1011 ---------------------------------------- Data padded with n-1 zeros : 1001101000 ---------------------------------------- CRC or Check value is : 101 ---------------------------------------- Final data to be sent : 1001101101 ---------------------------------------- Enter the received data: 1001101101 ----------------------------- Data received: 1001101101 No error detected Explanation There is no signal error since the data being transferred and received is identical. Enter the received data: 1001001101 ----------------------------- Data received: 1001001101 Error detected There is a signal error because the data sent and the data received are different. The execution time and space requirements of the program are represented by the time complexity and space complexity, respectively. The Big-O notation is used to represent the time and space complexity. Due to the fact that two for loops are inferred at once, the program's time complexity is O(n2). Due to the single dimension character array used to hold n characters, the programme has an O(n) space complexity. CRC Implementation using Bit ManipulationThe CRC program is implemented using bit manipulation techniques in this way. Algorithm The bit manipulation technique used to implement CRC in C is as follows:
The algorithm used to translate numbers from decimal to binary is as follows:
OUTPUT: Enter the data to be transmitted: 1001101 Enter the generator polynomial: 1011 Check value or CRC: 101 Data to be sent: 1001101101 ...................................... Process executed in 1.11 seconds. Explanation: The execution time and space requirements of the program are represented by the time complexity and space complexity, respectively. The Big-O notation is used to represent the program's complexity. The program's time complexity will be O(n) since only one for loop is assumed at a time, and its space complexity will also be O(n) because characters are stored in a single-dimensional character array. Conclusion:
Next TopicBinary search algorithm in C
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









