Database Assessment Tools for Kali Linux
As the amount of data generated by the business as well as the increasing number of attacks and database breaches, it is more important than ever to keep our data safe. Today's businesses ignore their databases, oblivious to the fact that gaining access to their data is one of a hostile individual's goals (typically their crown jewels). Freepik Heartland Payment Systems (worth $ 300 million), Talk Talk, and Archos are just a few of the well-known data breaches where the SQL injection vulnerability was used to obtain access to client data.
There are numerous advantages of carrying out a database security assessment. In Kali Linux, there are various tools that we can use to perform a database security assessment in our IT environment.
Advantages of Database security Assessments
A database security assessment examines the IT environment and identifies security vulnerabilities in databases, and examines the security controls implemented. The following are some of the advantages of conducting a database security assessment.
- It determines how successful security policies and procedures are.
- It enables a proactive security approach.
- It evaluates and verifies the security measures and mechanisms already implemented.
- It identifies security flaws and vulnerabilities in configurations and IT environments that can lead to data breaches, malicious infiltration, etc.
- It helps organizations to meet legal, regulatory, and compliance requirements such as
- It identifies security flaws and vulnerabilities in configurations and IT infrastructures, resulting in data breaches, hostile infiltration, and other problems.
Top 5 Database Security Assessment Tools on Kali Linux
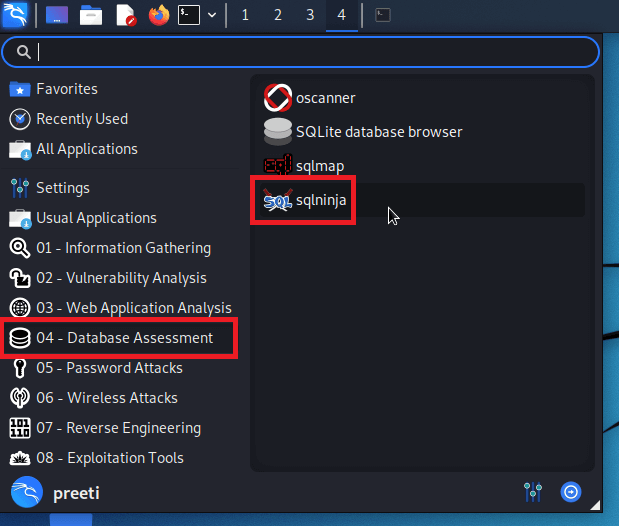
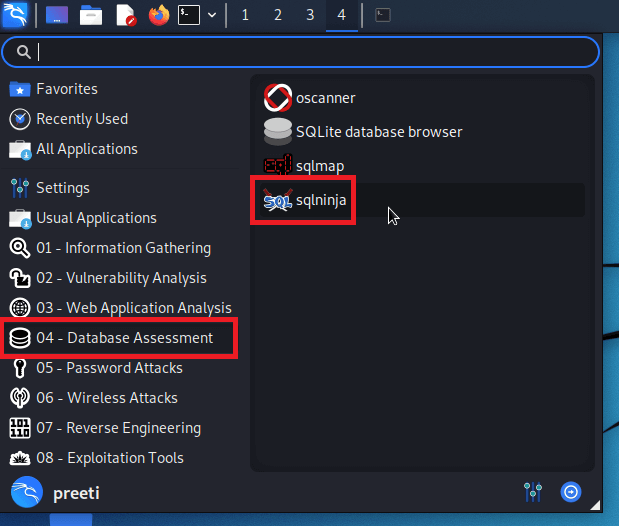
1. SQLNinja
SQLNinja is a specialized Perl-based tool that we used to exploit SQL injection vulnerabilities on a web application that uses Microsoft SQL server as its backend. It allows remove access to the vulnerable Database server and is used to help automate the process of taking over a DB Server when a SQL injection vulnerability is discovered.
Features of SQLNinja
The following are the features of SQLNinja:
- We can use this tool for data extraction.
- We can use this tool on Linux, FreeBSD, and Mac operating systems.
- We can use this tool from privilege escalation to the sysadmin group if the "sa" password has been found.
- It is used to upload executables via normal HTTP requests, vbscript, or exe.
- It is used to fingerprint the remote SQL server (including its version, user privileges, xp-cmdshell, a user performing the queries, and DB authentication mode).
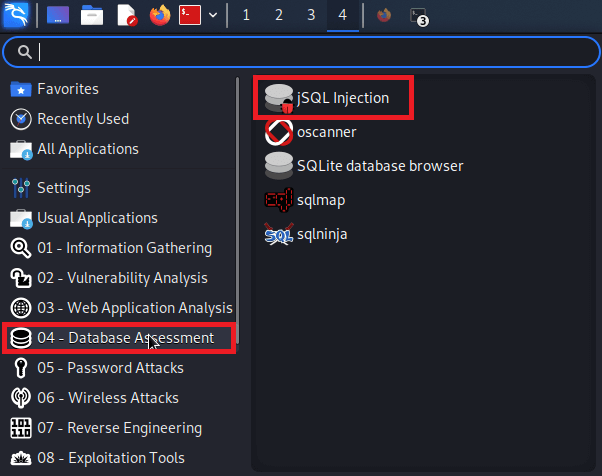
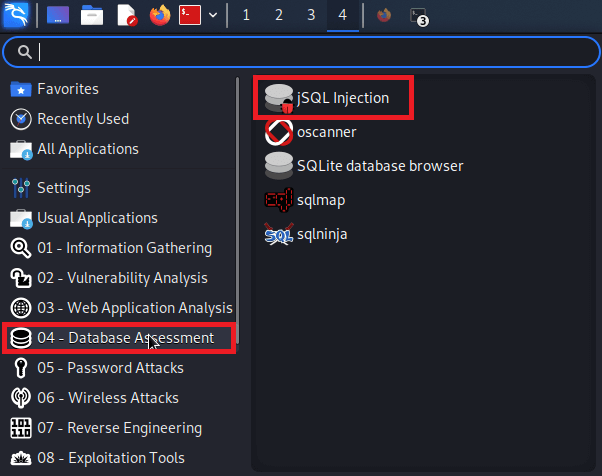
2. JSQL Injection
A java-based application called JSQL injection is used to retrieve database information from a remote server. It can be used to find and exploit SQL injections flaws.
Feature of JSQL Injection
The following are the features of JSQL Injection:
- The JSQL injection tool is used to brute-force hashes.
- The JSQL injection tool is used to search for admin pages.
- The JSQL injection can be used on Linux, Windows, and Mac operating systems.
- With the help of this tool, we can create a web shell and SQL shell on a remote host.
- It works with 33 different database engines, including Oracle, MSSQL. MYSQL, PostgreSQL, and others.
- With the help of this tool, we can hash, encode and decode text.
- It is used to authenticate using basic, NTLM, digest, and Kerberos.
- It performs several injection attacks like blind injection, time injection, normal injection, and error injection.
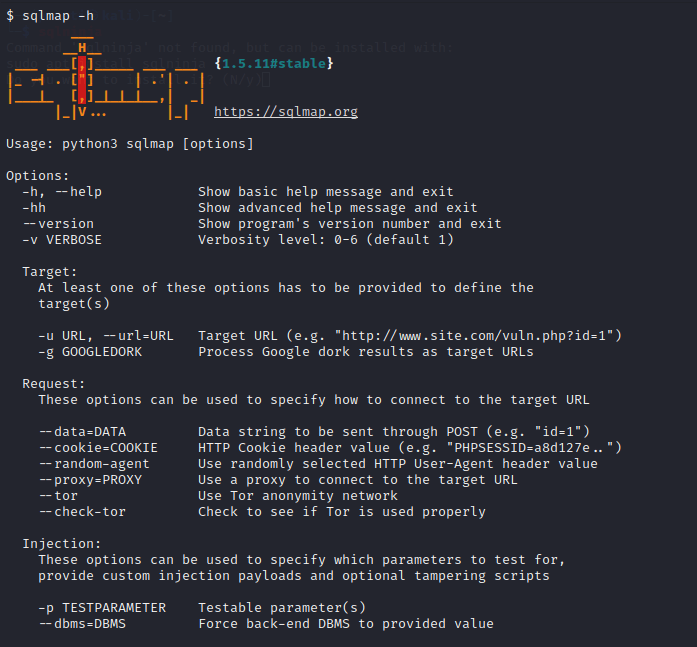
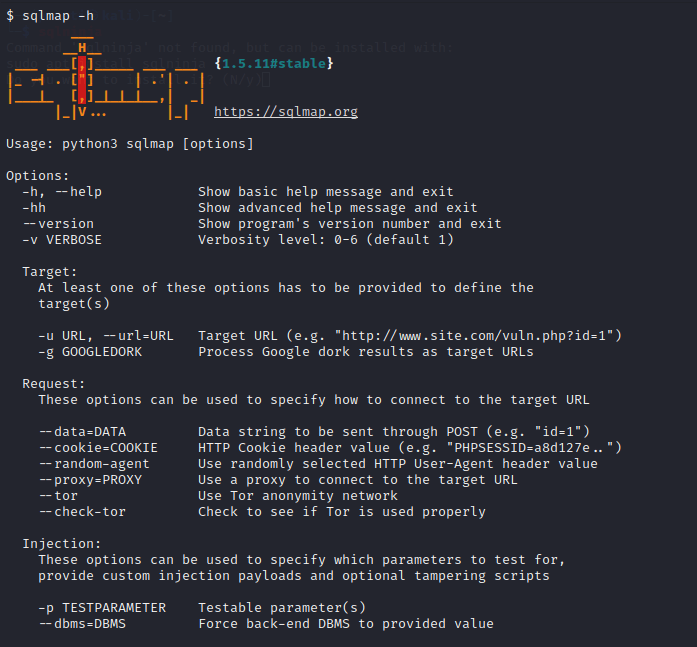
3. SQLMap
SQLMap is a Python-based SQL injection tool that is powerful and automatic. It is used to automate the process of finding and exploiting SQL injection flaws, as well as gaining complete control of database servers. It includes a robust detection engine, numerous features for the ultimate penetration tester, and a wide range of switches that span database fingerprinting, over data fetching from the database, accessing the underlying file system, and executing commands on the operating system via out-of-band connections.
Features of SQLMap
The following are the features of SQLMap.
- SQLMap is used to brute-force password hashes.
- We can use this tool to find and exploit several kinds of injection attacks like error-based SQL injection, stacked queries, time-based blind SQL injection, Boolean-based blind SQL, and UNION query SQL injection.
- SQLMap is used to run the arbitrary commands and retrieve their standard output (only works on MYSQL, PostgreSQL, and MSSQL servers).
- SQLMap is used to fingerprint the backend database software version as well as the underlying operating system.
- It supports several authentication protocols like Basic, NTLM, Digest, and
- We can use this tool to connect directly to the database without using SQL injection by providing the database details like DBMS credentials, port name, database name, and IP address.
- We can customize this tool.
- Support for dumping whole database tables, a range of entries, or selecting fields based on the user's preferences. The user can also select a subset of characters from each column's entry to dump.
- Automatic recognition of password hash formats and support for cracking them using a dictionary-based attack.
- Support for searching across all databases for specific database names, specific tables, or specified columns. It is helpful for identifying tables holding custom application credentials where the names of important columns comprise strings such as name and pass.
- We can use this tool to brute-force password hashes.
- Support to enumerate users, password hashes, tables, databases, columns, and
- Support for establishing an out-of-band stateful TCP connection between the attacker machine and the database server underlying the operating system. Depending on the user's preference, this channel can be an interactive command prompt, a Meterpreter session, or a graphical user interface (VNC) session.
- Support for user privilege escalation in database processes using Metasploit's Meterpreter getsystem
- SQLMap supports downloading and uploading any file from the database server underlying file system when the database software is MySQL, PostgreSQL, or Microsoft SQL Server.
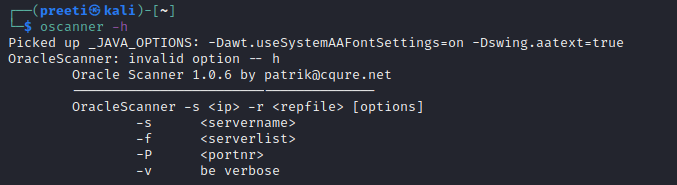
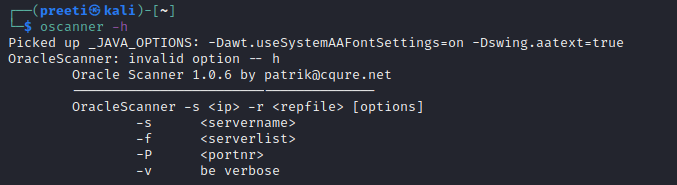
4. OScanner
OScanner is another tool that we used for database security assessment. OScanner is a java-based Oracle assessment framework. It comes with a number of useful plugins. The results are presented in the form of a graphical java tree.
Features of OSCanner
OScanner has the following features:
- OScanner is used for SID enumeration.
- We can use this tool to enumerate audit information and database links.
- OScanner is used to enumerate the version of Oracle, account privileges, account roles, and password policies.
- We can use tools for brute-forcing passwords.
5. BBQSQL
BBQSQL is a python-based open-source blind SQL injection framework. We use this tool for exploiting SQL injection vulnerability. Some standard request information must be provided as a SQL injection tool. The BBQSQL comprises various information such as HTTP Method, URL, Cookies, Headers, Files. Encoding, Redirect behavior, HTTP Auth, and Proxies. Then we must define where the injection will go as well as the syntax that will be injected. BBQSQL is a specialized tool that is extremely fast in detecting and exploiting hard-to-find and difficult-to-exploit blind SQL injection vulnerabilities in applications. Blind SQL differs from regular SQL injection in that it retrieves data from the database in a different method.
Features of BBQSQL
The following are the features of BBQSQL:
- BBQSQL is customizable.
- Database agnostic.
- We can use this tool to create a custom query and injection syntax.
- It is possible to use it to evaluate web apps and patch vulnerabilities found by the tool.
- Validates the input for all configuration options.
- BBQSQL needs some information before it can be used like URL, Headers, Cookies, HTTP Method, Encoding methods, etc.
- It is possible to configure BBQSQL in order to use either a binary or frequency search technique.
- BBQSQL is automatic and quick in detecting and exploiting hard-to-find and challenging blind SQL injection vulnerabilities present in an application.
- It can also be configured to look for certain values in the application's HTTP response to check if the SQL injection worked.
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now









