Features of Kali LinuxKali LinuxKali Linux is a Debian-based Linux distribution that comes with a number of pre-installed tools such as Nmap, Aircrack-ng, and Wireshark to help with information security tasks such as ethical hacking. If we are a security enthusiast or a beginner ethical hacker. Kali Linux was developed by a well-known information security company called Offensive Security. It is mainly designed for Digital forensic and Penetration testing. 
It is for those people who work in the cybersecurity and analysis fields. Kali Linux's official website is Kali.org. It became quite famous after appearing in Mr Robot series. It was not designed for general purposes; it should be used by professionals or individuals familiar with Linux/Kali. Kali Linux is used by professional penetration testers, ethical hackers, cybersecurity experts, and individuals who understand how to utilize Kali Linux. In other words, if you are familiar with Linux and its terminal commands, file management and architecture, and the system, then Kali Linux is a fantastic fit for you. And if you are not, we recommend that you start with the Ubuntu distribution to familiarize yourself with Linux and then move on to Kali Linux after some experience. This will not only save your time in searching the internet, but also you will be able to use it easily. On the other hand, Kali Linux is the best toolkit if you are a professional penetration tester or are learning penetration testing. Features of Kali Linux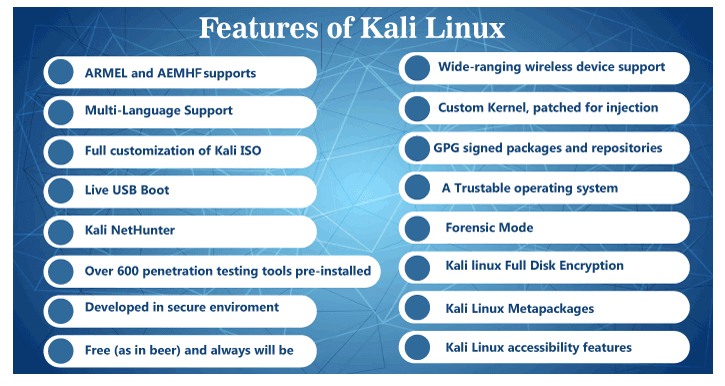
The following are the features of Kali Linux:
1. ARMEL and ARMHF SupportsSince ARM-based single-board systems such as Raspberry Pi and BeagleBone Black, among others, are becoming more and more prevalent and cheap, we know that Kali's ARM support needs to be as robust as possible, with completely working installations for both ARMEL and ARMHF systems. Kali Linux supports a wide range of ARM devices and has ARM repositories integrated with the mainline version, allowing ARM tools to be updated alongside the rest of the distribution. 2. Multi-Language SupportAlthough penetration tools are written in English, we've ensured that Kali comprises true multilingual support, permitting more users to work in their local language and locate the required tools. 3. Full Customization of Kali ISOsIt is always easy to generate a customized version of Kali for our specific needs using metapackages customized to a security professional's specific need sets and a highly accessible ISO customization process. Kali Linux is heavily integrated with live-build, giving us a lot of flexibility in customizing and modifying our Kali Linux ISO images. 4. Live USB BootThis enables us to install kali on a USB device and boot it without having to touch the host operating system (ideal for forensics work). With optional persistence volume(s), we can choose which file system Kali will use when it starts up, allowing files to be saved across sessions and numerous profiles to be created. Every persistent volume can be encrypted, which is a functionality that our industry requires; we also offer the LUKS nuke option, which allows us to regulate data destruction quickly. 5. Kali NetHunterKali on our (Android) phone. This includes a ROM overlay for many devices and the NetHunter App and NetHunter App Store. On top of this, we can also boot into a "full desktop" with the help of the chroot & containers, as well as "Kali NetHunter Desktop Experience (KeX)". 6. Over 600 Penetration Testing Tools Pre-installedKali Linux comprises more than 600 useful tools such as Crunch, Aircrak-ng, Wireshark, and Nmap. After analyzing each tool featured in BackTrack, Kali deleted many tools that either didn't operate or duplicated other tools that offered similar functionality. 7. Developed in Secured EnvironmentThe Kali Linux team consists of a small group of people who are the only ones allowed to commit packages and communicate with repositories, all of which is done through several secure protocols. 8. Free (as in beer) and Always Will beLike BackTrack, Kali Linux is and always will be absolutely free. We will never, ever have to pay for Kali Linux. 9. Wide-Ranging Wireless Device SupportA regular sticking point with Linux distributions has been supported for wireless interfaces. Kali Linux is designed to work with as many wireless devices as possible, enabling it to run on a wide range of hardware and connect with various USB and other wireless devices. 10. Custom Kernel, Patched for InjectionThe development team often needs to perform wireless assessments as penetration testers, so the Kernel includes the latest injection patches. 11. GPG Signed Packages and RepositoriesIn Kali Linux, each package is signed by each developer who built and committed it, and the repositories subsequently sign the packages as well. 12. A Trustable Operating SystemUsers of a security distribution want to know that it can be trusted and has been developed with a clear vision, permitting anybody to inspect the source code. Kali Linux is developed by a small group of skilled developers who operate transparently and follow best security practices: they upload signed source packages that are built on a dedicated build daemon. After that, the packages are checked for integrity and distributed as part of a signed repository. The work done on the packages can be thoroughly reviewed using the Kali source package packaging Git repositories (comprising signed tags). The Kali package tracker can also be used to trace the evolution of each package. 13. Forensics ModeIn general, when we are performing forensic work on a system, we should avoid doing anything that can change the data on the analyzed system in any manner. However, modern desktop environments tend to obstruct this goal by attempting to auto-mount any disk(s) they identify. Kali Linux offers a forensics mode that may be enabled from the boot menu to prevent this behavior: it disables all such functions. The live system is mainly helpful for forensics purposes because any computer can be rebooted into a Kali Linux system without accessing or altering its hard discs. 14. Kali Linux Full Disk EncryptionKali Linux LUKS Full Disk Encryption (FDE)- The ability to encrypt the whole hard drive of our critical penetration testing computer drive is a vital feature needed in the industry. 15. Kali Linux MetapackagesMastering Kali Linux tool sets with Kali Metapackages-Kali includes a number of meta-package collections that combine various toolsets. This makes it simple to get custom, minimized environments set up. For example, we can apt-get install kali-Linux-wireless if all we need is some wireless utilities for an impending evaluation. 16. Kali Linux Accessibility FeaturesThis feature is mainly for visually impaired users- Kali is one of the few Linux distributions that include both voice feedback and braille hardware support for blind or visually impaired users. Advantages of Kali LinuxThere are various advantages of Kali Linux:
Disadvantages of Kali LinuxThere are various disadvantages of Kali Linux:
Next TopicUse of Kali Linux
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









