Vulnerability Scanning in Kali LinuxIf we want to know what vulnerability scanning is, then first, we have to know what vulnerability is. So, in the field of Cyber Security, vulnerability means the weakness of the computer system that an attacker can exploit to execute unauthorized operations or gain unauthorized operations or gain unauthorized access to a system. The attacker can perform nearly anything with the system, including data breaching (stealing sensitive information), malware installation, and so on. Let's look at vulnerability scanning in more detail. Vulnerability scanning is the process of searching for vulnerabilities in a computer system. A vulnerability scanner is used to perform this task. A vulnerability scanner is a software designed for testing applications or computers for vulnerabilities. It finds and creates a directory for each process connected to the system (e.g. Firewall, networks, servers, etc.) Misconfigurations and faulty programming within a network are used to identify vulnerabilities. The possibility of risks in a system is determined by the vulnerabilities present. Working of Vulnerability ScanningA three-step process is used to scan for vulnerabilities. The following are the details:
Vulnerabilities IdentificationThe vulnerability scanner can identify vulnerabilities. The vulnerability scanner's effectiveness is determined by its capacity to acquire information on the system, find open ports, devices, etc. Analysis of the Risk Possessed by Vulnerabilities FoundThis phase is important for the team performing vulnerability scanning. This step decides:
Operations Against the identifies VulnerabilityThe vulnerabilities identified by the scanner should be fixed or patches so that they can no longer cause harm to the system or be exploited by an attacker. However, because a simple fix for the vulnerability is not available, we have two options:
Types of Scanning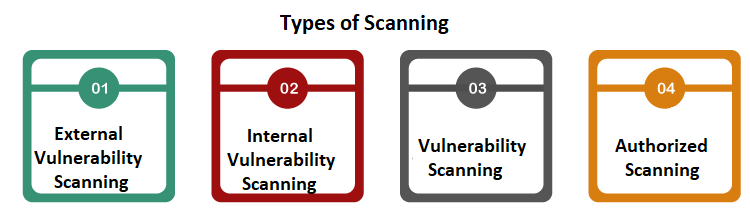
The following are the types of scanning: 1. External Vulnerability Scanning External vulnerability scanning is performed from outside the organization's network. This scan focuses on areas that have internet access or application that external users or customers use. 2. Internal Vulnerability Scanning Internal vulnerability scanning is performed from inside the organization. Its goal is to successfully find and detect flaws that an attacker could exploit. An attacker can be anyone attempting to obtain unauthorized access or internal workers with access to the organization's critical information. 3. Unauthorized Scanning Unauthorized scanning searches for vulnerabilities within an organization's network perimeter. 4. Authorized Scanning Authorized scanning enables vulnerability scanners to probe inside a network by offering them privileged credentials to check for weak passwords, misconfigured, flawed programming of applications, or misconfigured databases. Security MeasuresThe cybersecurity team has taken the following security measures to ensure that vulnerabilities and malware are less likely to be discovered by any type of attack. 1. Breach and Attack Simulation (BAS) Technology The BAS technology is often used as an attacker to test network security. The tools perform several scans and attacks to assess the capabilities of the targeted network's defense in terms of prevention, detection, and efficiency. 2. Application Security Testing Application security testing is performed to ensure that the application is working properly, to prevent sensitive data from being exposed to external threats, and to check the misconfiguration in the code of the application. It is carried out in order to assess the application's security as well as its flaws and vulnerabilities. It aids in the detection and prevention of vulnerabilities being exploited. Vulnerability ScannersThe following is the list of open-source vulnerability scanners:
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









