Grim-Information Gathering Tool in Kali LinuxIn Kali Linux, Grim is a free and open-source tool that is available on GitHub. We used this tool to scan websites for information gathering and finding vulnerabilities. Grim is written in PHP. It performs reconnaissance using a PHP script. Grim is a powerful tool because it can detect IP addresses, it can detect Content Management Systems while scanning, it can detect robots.txt, it can detect webserver records, and it can detect cloud flare information. Grim can also detect Drupal, Magento CMS, and WordPress. Grim looks for error-based SQL injections, WordPress sensitive files, and WordPress version-related vulnerabilities. Grim performs all of the scans with the help of the various modules. The WHOIS data collection gives us information related to the Geo-IP lookup, DNS lookup, Banner grabbing, Sub-domain information, reverse IP, port scanning, and MX records lookup. How to Install Grim in Kali LinuxThe following are the steps that we used to install Grim in Kali Linux: Step 1: First, we have to use the command below in order to install the tool from GitHub. 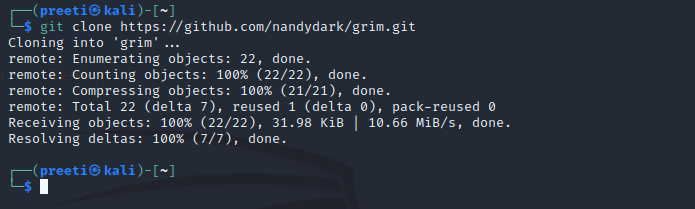
Step 2: Now, we have to move in the tool's directory with the help of the following command. 
Step 3: After the tool has been successfully downloaded, start it with the command below. 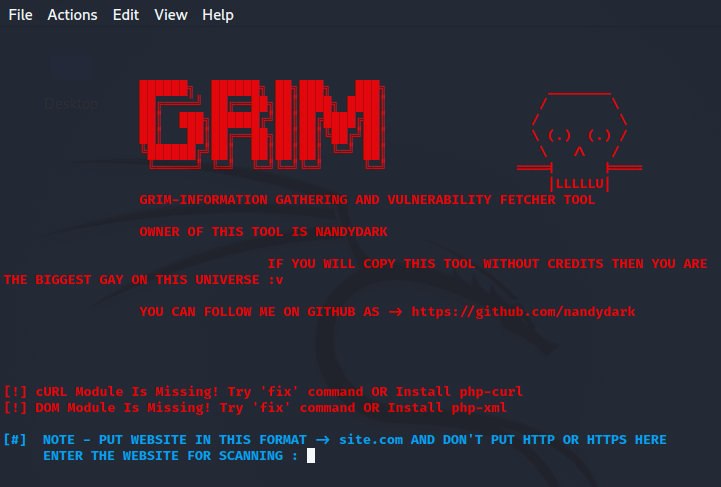
The tool is working properly. Now the tool is asking for a website to set a target, we will look at some instances to understand how to use Grim tool. How to use the Grim Tool in Kali LinuxLet's look at some instances to learn how to use grim tool in kali Linux: Example 1: We can use the grim tool in order to find the information related to the domain. Use the following command to find the information about a domain. 
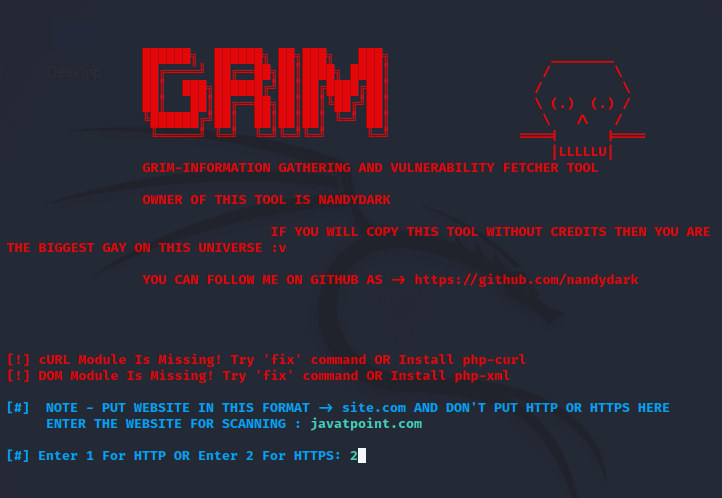
We have given the tool the domain javatpoint.com. The tool will now begin scanning the domain and provide us with all the relevant information about the domain. The tool discovered numerous domain subdomains as well as the IP address linked with the domain address. This tool is finding SQL injection flaws. This tool will collect as much information on the domain we specified as publicly available one by one. In the early stages of security research, this tool is really useful. 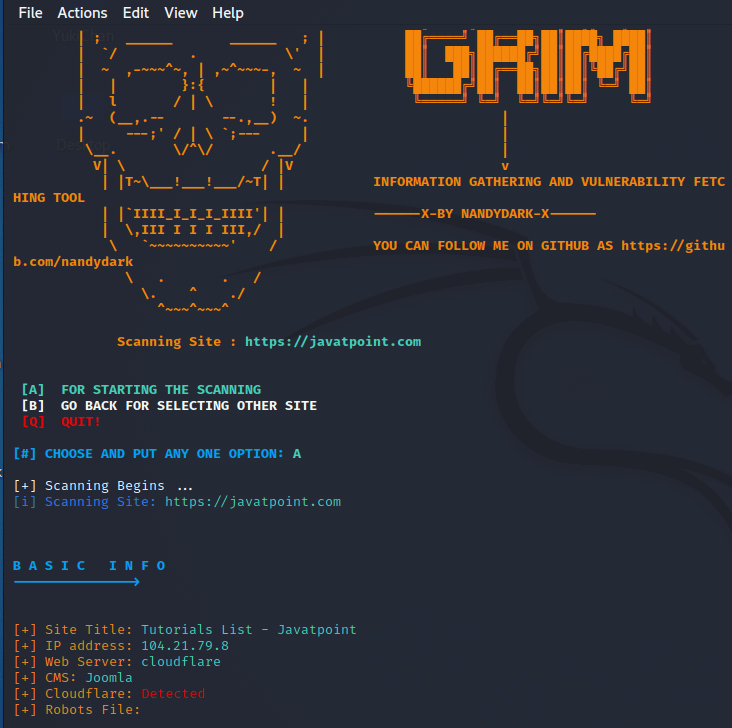
Next TopicVulnerability Scanning in Kali Linux
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









