Seven Layers of IT SecurityThis article will help you in providing a good understanding of the seven layers of IT security. Before moving on to the main topic first let us know what are IT security layers. What are IT security Layers?IT security layers refer to the several levels of security controls that may be used to defend against online attacks. As we know, there are many other alternatives, but the "defence in depth" paradigm is a typical framework for layering cybersecurity measures. To provide a more thorough and effective defence against cyber-attacks, this concept entails putting in place many layers of security measures. Layers of IT securityThere are seven layers of IT security that are mentioned and explained below: Layer1- Mission critical assets Layer2- Data security Layer3- Application Security Layer4- Endpoint Security Layer5- Network Security Layer6- Perimeter Security Layer7- The Human layer 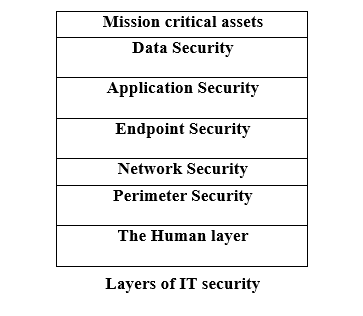
Let us understand each layer from the bottom to the top manner. Layer 7 - The Human LayerHumans alone are responsible for 90% of data breaches, making them the weakest link in any cyber security strategy. Human security includes the following measures:
Security Plan: The greatest approaches to keep the human layer safe comes under the education and training. This includes guidelines on how to spot and respond to phishing attempts, strong password techniques, system hardening, and cyber security awareness. Access restriction is a good idea for safeguarding the human layer since they can lessen the potential damage from a successful assault. Layer 6 - Perimeter SecurityThe perimeter security controls have digital and physical security measures that protect the entire business. When identifying the type of data being transferred across this layer, we must first determine our perimeter. After that, we must secure both data and the device. Security Plan: Installation of firewalls, data encryption, antivirus software, and device management are the security strategies which are crucial when a company allows their employees to use their own device. This layer also establish a safe demilitarised zone to enhance security. Layer5 - Network SecurityThere are various methods of network security used to protect a company's network and helps in preventing unauthorized access. The main concern with the network layer is what people and devices may access once they are on a network. Network Security methods/techniques are mainly used to protect the important data of an organization from network attacks. Security Plan: If no individual has access to everything, then any successful hack only compromises a tiny piece of the network. At this stage, the security measures only allow the devices and workers to access only those network resources that are essential for them to perform their tasks. Layer4 - Endpoint SecurityAny device that is linked to your network is referred to as an endpoint. As we mentioned above, there are so many endpoints on networks nowadays that it may be a bit daunting. To manage and monitor these devices, it is crucial to present the robust policy. Security Plan: At this level, encryption is essential, but it can't merely apply to your data. To make sure that the devices themselves are operating in safe settings, endpoint encryption must be installed. Layer3 - Application SecurityThis layer of IT security covers all the programs and applications which are using by the user. Various programs like Microsoft Office, Teams, Zoom, and others, which performs our daily tasks would be secured. Security Plan: In this situation, the simplest thing you can do to update your programs or applications regularly. Due to this, it is possible to secure and safe the application and also helps in ensuring that the existing security flaws are fixed. In this stage, the security measures will use sandboxes for browser-based applications and the software restriction guidelines to prevent the unauthorised software which is being executed on your network. Along with this, we can safe the things by using the next-generation firewalls which are working with the integrated app protection. Layer2 - Data SecurityCybercriminals mainly target the data in almost every instance. This layer mainly deals with providing high security to the data. As, the data is considered as heart and soul for a business. Your company's specific needs will determine the type of data you have, but it may include customer information, payment information, social security numbers, trade secrets (and other intellectual property), and healthcare data. Security Plan: At this stage, file and disc encryption, regular backups of all crucial data and operations, two-factor authentication, enterprise rights management, and policies are ensuring that data is deleted from inactive devices or that are being given to another person for use. Layer1 - Mission Critical AssetsAnything without which your company cannot thrive is listed here. This covers operating systems, cloud infrastructure, software tools, and electronic health records. The difficulty at this layer is that what is crucial for one business may not be crucial for yours. To secure your business, you must first identify the essential elements of it. Security Plan: In this level, you have to decide the important apsects to your business.
Next TopicWhat is Ad Hoc TCP
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









