What is Tree Topology?A tree topology is a sort of structure in which each node is related to the others in a hierarchy. In a topological hierarchy, there are at least three distinct levels. Sometimes it is also called hierarchical topology as in this topology, all elements are arranged like the branches of a tree. It is a lot like the star and bus topologies. Tree topologies are commonly used to arrange data in databases and workstations in corporate networks. In a tree topology, any two linked nodes can only have one mutual connection, hence there can only be one link between them. 
There are several ways to define tree topology; such are as follows:
The disadvantage of a tree topology is that if the primary node is damaged, the entire system can be crippled, because all other nodes are connected to the primary node. Tree Topology in Computer NetworkIn computer networks, a tree topology is sometimes known as a star bus topology because it combines features of both star and bus topologies to create a tree-like structure. In this topology, every branch contains Star Network, and its main structure is designed in the form of a bus backbone cable. Therefore, the primary bus is attached to one or more buses and switches, which further connects to one or more Network Devices and Network Nodes. It is a very flexible computer networking method that allows you to add Network Devices to this network by simply expanding the Star Network at each branch of a tree. However, you may need to add or remove devices at certain times. Tree Topology Examples in Real LifeIf you have small sub-departments or departments and, this topology is very useful. Similarly, it can be the best choice for you if you have a multi-floor team placement. If you try to utilise the basic Star Network plan, you may run into a lot of issues since it is not always reasonable; in certain cases, it can be more expensive. Similarly, you will be unable to acquire a basic bus network as it needs the installation of bus backbone cables. It will also necessitate a large number of punctures in Backbone and Sub Backbone Cables. It is, however, quite expensive. If you install more network nodes in a department or sub-department, you'll need to puncture backbone cables at various locations, which might reduce network performance. Therefore, you will need to use a strong cable to connect floors. Furthermore, each departmental and sub-departmental network Nodes will connect to a single Hub, which will be located inside both departments. If you arrange it like this, it will be more affordable and effective. As compared to basic types of Network Topology, it is more reliable, fault-tolerant, and flexible. You can get many problems if you use a simple Star Network or Bus Network. Therefore, the use of the hybrid scheme is more beneficial for facilitating yourself. Applications and Uses of Tree TopologyAlthough tree topology has no common applications to use, however, its use is totally dependent on users. You can get benefit from it as well as using it. Zigbee comes under the application of the Tree Topology network. But the fact is that Zigbee does not use Tree Topology. However, you can use it anywhere in terms of networking.
Features of Tree Topology
How Tree Topology Network Works?The below image will help you to understand how Tree Topology works. 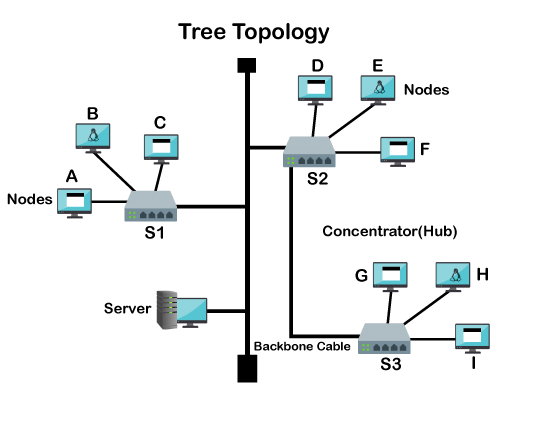
For example, if the server wants to establish a connection to Node I, it will digest or encapsulate the destination address and data. Then, it will transmit the signal to Backbone Cable after completing the encapsulation process. The encapsulated package will start to pass on both sides of branches of the Bus Backbone Network. There are three types of Hub that can be used in the Three Topology Network, which are Intelligent Hub, Active Hub, and Passive Hub. They all contain their own working mechanism. We are explaining only the working process of an Intelligent Hub. Let's consider that all Hubs are Intelligent, which is Switch. The packet will first go to Switch S1, which will examine the packet's destination address after receiving it. It will automatically discard the package if the destination address does not match this portion. Similarly, the encapsulated packet will reach Switch S2, which will check the destination address. If it finds the destination address does not match, it will send the package to Switch S3. Then, S3 will find the link that connects the destination address and forward the package to the specified destination. Types of Tree TopologyAlthough the types of tree topology are not specialized, people should also know about these types. These types may help you in your networking career.
Advantages of Tree TopologyThere are numerous benefits of the tree topology, which are as follows:
Disadvantages of Tree TopologyThe tree topology has some disadvantages, which are as follows: Dependent on the main bus cableA tree topology depends upon a cable to transmit data to the whole network as the information is passed one to one node that creates weak areas. If one node has been damaged, it will impact the entire network, and the rest of the network will be inaccessible. It becomes more difficult if the event occurs in the backbone cable. Furthermore, if a defect happens before the remainder of the tree topology's branches, the complete system will not function correctly. Even if all devices on the other side of the problem can still communicate with each other. Maintaining the network can be a challengeIt might be tough to keep a network up and running when there are multiple nodes and trees. Once adequate scalability is achieved in tree topology, the network's size might begin to act against it. It consumes more time to maintain one-to-one node connections, manage the individual stars, and investigate faults. When only one backbone cable is utilised to deliver services and a large number of peripherals and terminals are in use, the network's speed might suffer. Tree topologies must usually follow the 5-4-3 ruleGenerally, it follows the 5-4-3 rule that occurs when the tree topology network is created with the help of the Ethernet protocol. This protocol needs that a transmitted signal must reach within a specific time every part of the network. A signal used to distribute data by every concentrator or repeater will add more time to the network. It means only a maximum of five segments can be available between any two nodes, which are connected with the help of four concentrators or repeaters. If the segments are made of coaxial cable, only three of the segments may be populated. This disadvantage does not occur where fiber backbones or fiberoptic cabling are present or to another type of network topology. Scalability depends on the type of cable usedIn tree topology, a cable type and length that is used to create the point-to-point connections may become disadvantage for network. If you create the system in the first place, you are naturally limited in each segment to use the cable length and type. Therefore, as compared to other topologies, this option is most difficult to configure and wire. If you want to system with limitless scalability, it will be more costly when pursuing this design. Installation difficultThe installation of tree topology might be challenging since it uses star and bus configuration principles when designed with linear characteristics; hence, this choice produces the most complex installation procedure. When deciding what topology to use, the cost is a common factor. The initial investment in tree topology can be substantial, as the tree topology's cabling needs include bus and star topology requirements. Security issues with Tree TopologyOne of the biggest disadvantages of a tree topology is a security issue as all workstations connected in the network of tree topology can see the sent data along with the network. When all of the connections are up and running, they all have access to each other, making the system less secure. If any unauthorized person can enter the building and access the network, they can destroy the entire network within a few seconds. Therefore, it can be more harmful to any business or other that uses tree topology. To protect their information, they must include workstation-based security protocols and other password protections to prevent information access. You can also prevent unauthorized access by applying physical security at the front door. Some key factors of disadvantages of tree topology are also given below:
Next TopicWhat is Scanner
|
 For Videos Join Our Youtube Channel: Join Now
For Videos Join Our Youtube Channel: Join Now
Feedback
- Send your Feedback to [email protected]
Help Others, Please Share









